APPLICATIONS
HOT NEWS
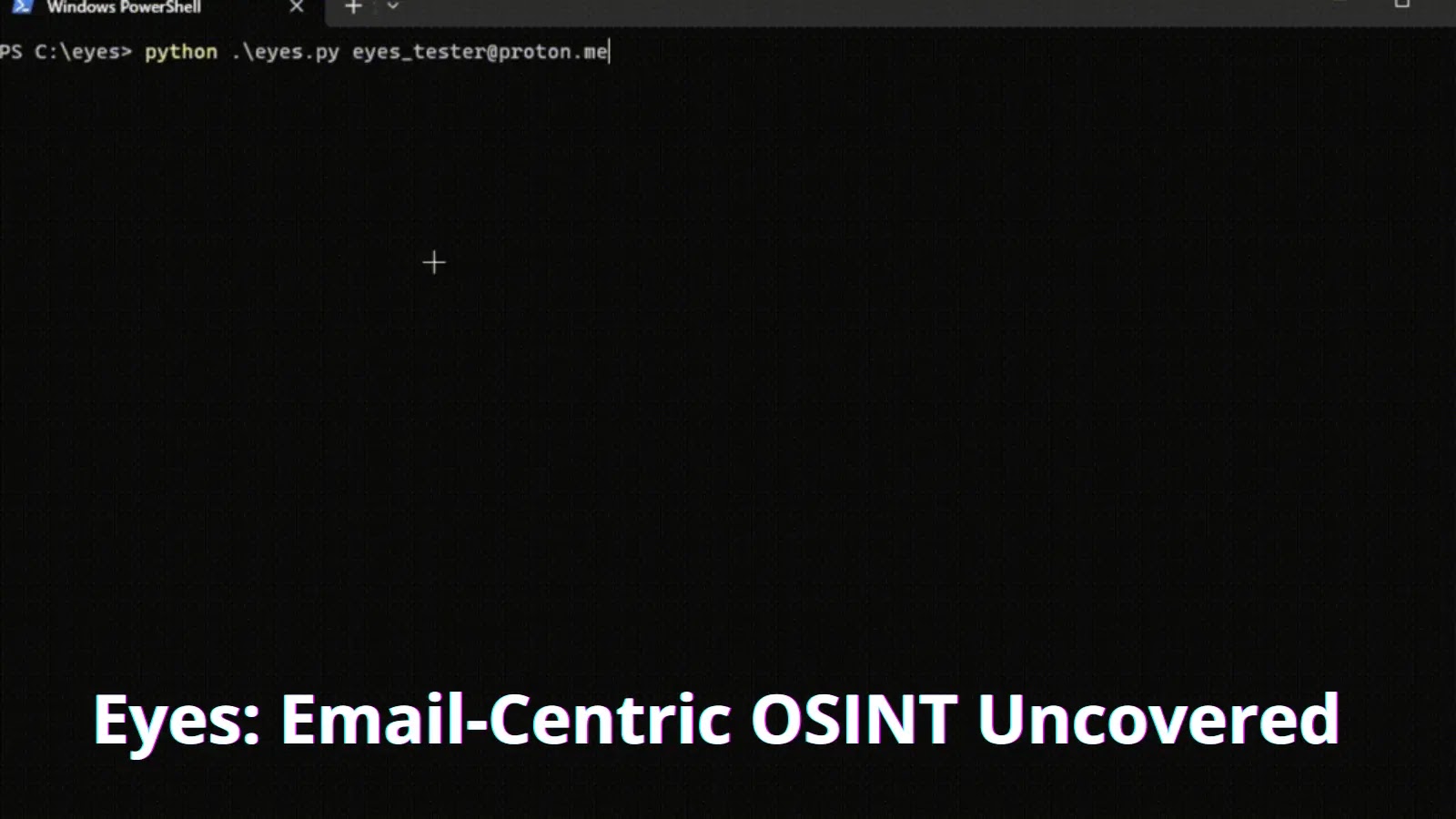
Eyes: Email-Centric OSINT Uncovered
Eyes is an OSINT tool that focuses on extracting information related to an email address.
Whether you’re a cybersecurity professional, a private investigator, or...
© kalilinuxtutorials.com 2025