APPLICATIONS
HOT NEWS
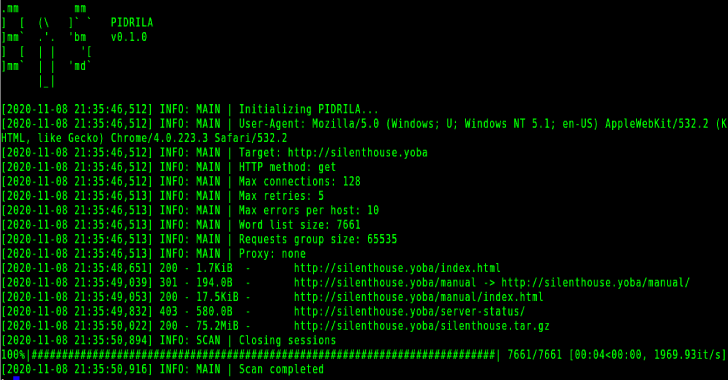
Pidrila : Python Interactive Deepweb-Oriented Rapid Intelligent Link Analyzer
Pidrila is a Python Interactive Deepweb-oriented Rapid Intelligent Link Analyzer is really fast async web path scanner prototype developed by BrightSearch team for all...
© kalilinuxtutorials.com 2025