DalFox is just XSS Scanning and Parameter Analysis tool. I previously developed XSpear, a ruby-based XSS tool, and this time, a full change occurred during the process of porting with golang!!! and created it as a new project. The basic concept is to analyze parameters, find XSS, and verify them based on DOM Parser.
I talk about naming. Dal(달) is the Korean pronunciation of moon and fox was made into Fox(Find Of XSS).
Key Features
- Paramter Analysis (find reflected parameter, find free/bad characters, Identification of injection point)
- Static Analysis (Check Bad-header like CSP, X-Frame-optiopns, etc.. with base request/response base)
- Optimization query of payloads
- Check the injection point through abstraction and generated the fit payload.
- Eliminate unnecessary payloads based on badchar
- XSS Scanning(Reflected + Stored) and DOM Base Verifying
- All test payloads(build-in, your custom/blind) are tested in parallel with the encoder.
- Support to Double URL Encoder
- Support to HTML Hex Encoder
- Friendly Pipeline (single url, from file, from IO)
- And the various options required for the testing 😀
- built-in / custom grepping for find other vulnerability
- if you found, after action
- etc..
Also Read – Shellerator : CLI Tool For The Generation Of Bind & Reverse Shell
How To Install?
There are a total of three ways to Personally, I recommend go install.
Developer version (go-get or go-install)
go-install
- clone this repo
$ git clone https://github.com/hahwul/dalfox
- install in cloned dalfox path
$ go install
- using dalfox
$ ~/go/bin/dalfox
go-get
- go get dalfox!
$ go get -u github.com/hahwul/dalfox
- using dalfox
$ ~/go/bin/dalfox
Release Version
- Open latest release page https://github.com/hahwul/dalfox/releases/latest
- Download file Download and extract the file that fits your OS.
- You can put it in the execution directory and use it. e.g
$ cp dalfox /usr/bin/
Usage
Parameter Analysis and XSS Scanning tool based on golang
Finder Of XSS and Dal is the Korean pronunciation of moon. @hahwul
Usage:
dalfox [command]
Available Commands:
– file Use file mode(targets list or rawdata)
– help Help about any command
– pipe Use pipeline mode
– sxss Use Stored XSS mode
– update Update DalFox (Binary patch)
– url Use single target mode
– version Show version
Flags:
-b, –blind string Add your blind xss (e.g -b hahwul.xss.ht)
–config string Using config from file
-C, –cookie string Add custom cookie
–custom-payload string Add custom payloads from file
-d, –data string Using POST Method and add Body data
–delay int Milliseconds between send to same host (1000==1s)
–found-action string If found weak/vuln, action(cmd) to next
–grep string Using custom grepping file (e.g –grep ./samples/sample_grep.json)
-H, –header string Add custom headers
-h, –help help for dalfox
–ignore-return string Ignore scanning from return code (e.g –ignore-return 302,403,404)
–only-discovery Only testing parameter analysis
-o, –output string Write to output file
–output-format string -o/–output ‘s format (txt/json/xml)
-p, –param string Only testing selected parameters
–proxy string Send all request to proxy server (e.g –proxy http://127.0.0.1:8080)
–silence Not printing all logs
–timeout int Second of timeout (default 10)
–user-agent string Add custom UserAgent
-w, –worker int Number of worker (default 40)
$ dalfox [mode] [flags]
Single target mode
$ dalfox url http://testphp.vulnweb.com/listproducts.php\?cat\=123\&artist\=123\&asdf\=ff -b https://hahwul.xss.ht
Multiple target mode from file
$ dalfox file urls_file –custom-payload ./mypayloads.txt
Pipeline mode
$ cat urls_file | dalfox pipe -H “AuthToken: bbadsfkasdfadsf87”
Other tips, See wiki for detailed instructions!
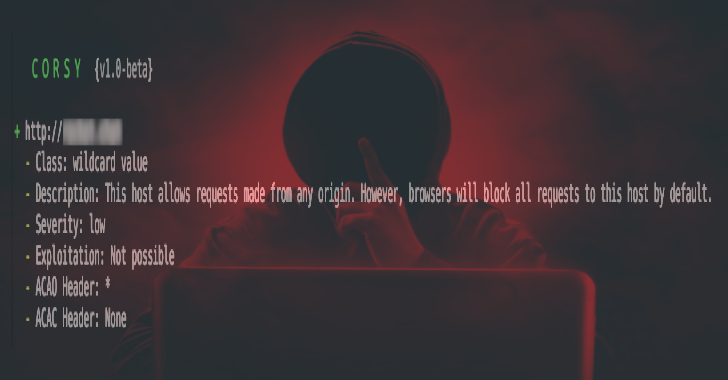
ScreenShot