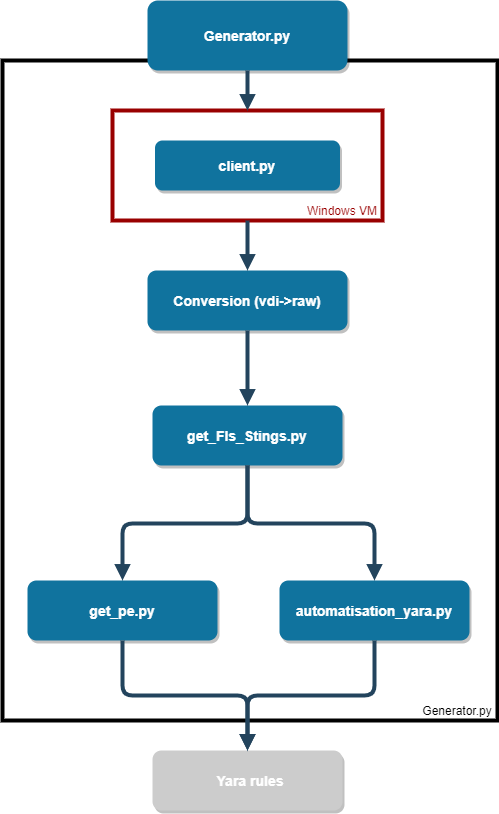
Factual-rules-generator is an open source project which aims to generate YARA rules about installed software from a running operating system.
The goal of the software is to be able to use a set of rules against collected or acquired digital forensic evidences and find installed software in a timely fashion.
The software can be used to baseline known software from Windows system and create a set of rules for finding similar installation on other systems.
Dependencies
- pefile
- psutil
- ndjson
- python-tlsh
- PyInstaller (to change client.py to client.exe)
- ssdeep
- On Ubuntu:
sudo apt-get install build-essential libffi-dev python3 python3-dev python3-pip libfuzzy-devpip install ssdeep
- On Ubuntu:
Tools requirement
Some tools are required on the host operating system some are Unix standard tools and some additional ones:
- xxd
- curl
For the Windows virtual machine, the following software is required to be installed:
- SDelete
- AsA (AttackSurfaceAnalyzer)
Install
- Install all Python dependencies defined requirements.txt
- Create a shared folder to communicate with VM
- Install a Windows VM
- Install chocolatey on Windows VM
- Complete
bin/OnWindows/Varclient.py - Change
bin/OnWindows/client.pyin an executable file with PyInstaller and put in startup folder
- Update
etc/allVariables.pyto match your desired configuraiton
In test/ some examples of software to install is given, the following specific format is required:
- First, select the name of the packages to install using chocolatey before
:, or the name of the file in case of msi or exe file. - Second, after
:there’s the name of the exe to extract and run it (without extension). - The second part after
,follow the same system with the wordinstallerfirst and after:the type of installer :- choco
- msiexec
- exe
- Finally, the third part,
uninstallerfollow by:and the uninstaller like choco, msiexec or exe
Run and generate the rules
bin/Generator.pyis the only script to run, don’t forget to updateetc/allVariables.py(critical step).
Public YARA rules repository
- factual-rules – Sample rules generated from some very common software.
Overview of factual rules generator






.png)