Fwknop implements an authorization scheme known as Single Packet Authorization (SPA) for strong service concealment.
SPA requires only a single packet which is encrypted, non-replayable, and authenticated via an HMAC in order to communicate desired access to a service that is hidden behind a firewall in a default-drop filtering stance.
The main application of SPA is to use a firewall to drop all attempts to connect to services such as SSH in order to make the exploitation of vulnerabilities (both 0-day and unpatched code) more difficult.
Because there are no open ports, any service that is concealed by SPA naturally cannot be scanned for with Nmap.
The fwknop project supports four different firewalls: iptables, firewalld, PF, and ipfw across Linux, OpenBSD, FreeBSD, and Mac OS X.
There is also support for custom scripts so that fwknop can be made to support other infrastructure such as ipset or nftables.
SPA is essentially next generation Port Knocking (PK), but solves many of the limitations exhibited by PK while retaining its core benefits.
PK limitations include a general difficulty in protecting against replay attacks, asymmetric ciphers and HMAC schemes are not usually possible to reliably support.
It is trivially easy to mount a DoS attack against a PK server just by spoofing an additional packet into a PK sequence as it traverses the network (thereby convincing the PK server that the client doesn’t know the proper sequence).
All of these shortcomings are solved by SPA. At the same time, SPA hides services behind a default-drop firewall policy, acquires SPA data passively (usually via libpcap or other means), and implements standard cryptographic operations for SPA packet authentication and encryption/decryption.
SPA packets generated by fwknop leverage HMAC for authenticated encryption in the encrypt-then-authenticate model. Although the usage of an HMAC is currently optional (enabled via the --use-hmac command line switch), it is highly recommended for three reasons:
- Without an HMAC, cryptographically strong authentication is not possible with fwknop unless GnuPG is used, but even then an HMAC should still be applied.
- An HMAC applied after encryption protects against cryptanalytic CBC-mode padding oracle attacks such as the Vaudenay attack and related trickery (like the more recent “Lucky 13” attack against SSL).
- The code required by the fwknopd daemon to verify an HMAC is much more simplistic than the code required to decrypt an SPA packet, so an SPA packet without a proper HMAC isn’t even sent through the decryption routines.
The final reason above is why an HMAC should still be used even when SPA packets are encrypted with GnuPG due to the fact that SPA data is not sent through libgpgme functions unless the HMAC checks out first.
GnuPG and libgpgme are relatively complex bodies of code, and therefore limiting the ability of a potential attacker to interact with this code through an HMAC operation helps to maintain a stronger security stance.
Generating an HMAC for SPA communications requires a dedicated key in addition to the normal encryption key, and both can be generated with the --key-gen option.
fwknop encrypts SPA packets either with the Rijndael block cipher or via GnuPG and associated asymmetric cipher.
If the symmetric encryption method is chosen, then as usual the encryption key is shared between the client and server (see the /etc/fwknop/access.conf file for details).
The actual encryption key used for Rijndael encryption is generated via the standard PBKDF1 key derivation algorithm, and CBC mode is set. If the GnuPG method is chosen, then the encryption keys are derived from GnuPG key rings.
Also Read : Security Analysis Toolkit For Car Protocols – CANalyzat0r
Use Cases
People who use Single Packet Authorization (SPA) or its security-challenged cousin Port Knocking (PK) usually access SSHD running on the same system where the SPA/PK software is deployed.
That is, a firewall running on a host has a default-drop policy against all incoming SSH connections so that SSHD cannot be scanned, but a SPA daemon reconfigures the firewall to temporarily grant access to a passively authenticated SPA client:
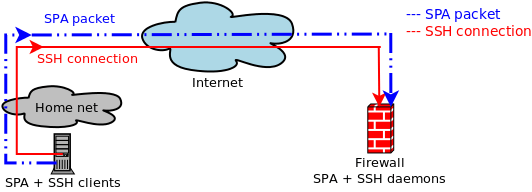
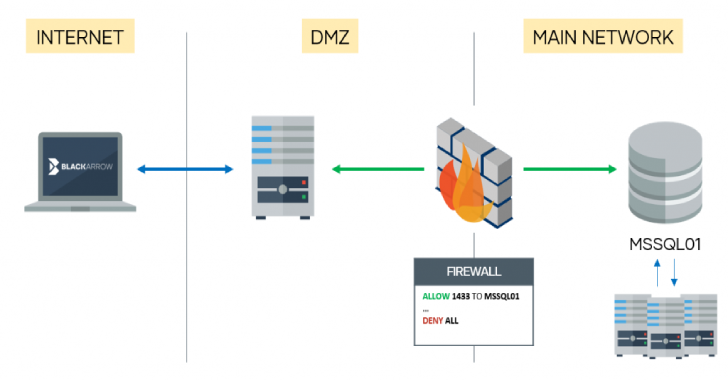
fwknop supports the above, but also goes much further and makes robust usage of NAT (for iptables/firewalld firewalls).
After all, important firewalls are usually gateways between networks as opposed to just being deployed on standalone hosts.
NAT is commonly used on such firewalls (at least for IPv4 communications) to provide Internet access to internal networks that are on RFC 1918 address space, and also to allow external hosts access to services hosted on internal systems.
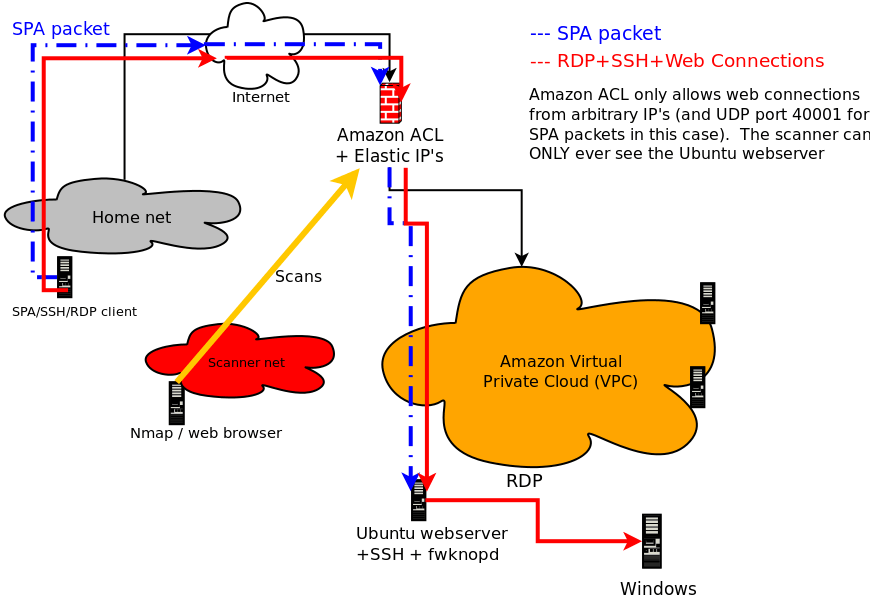
Because fwknop integrates with NAT, SPA can be leveraged to access internal services through the firewall by users on the external Internet.
Although this has plenty of applications on modern traditional networks, it also allows fwknop to support cloud computing environments such as Amazon’s AWS:
“SPA usage on Amazon AWS cloud environments”.
User Interface
The official cross-platform fwknop client user interface fwknop-gui (download, github) is developed by Jonathan Bennett.
Most major client-side SPA modes are supported including NAT requests, HMAC and Rijndael keys (GnuPG is not yet supported), fwknoprc stanza saving, and more.
Currently fwknop-gui runs on Linux, Mac OS X, and Windows – here is a screenshot from OS X:

“fwknop-gui on Mac OS X” Similarly, an updated Android client is available as well.
Features
The following is a complete list of features supported by the fwknop project:
- Implements Single Packet Authorization around iptables and firewalld firewalls on Linux, ipfw firewalls on *BSD and Mac OS X, and PF on OpenBSD.
- The fwknop client runs on Linux, Mac OS X, *BSD, and Windows under Cygwin. In addition, there is an Android app to generate SPA packets.
- Supports both Rijndael and GnuPG methods for the encryption/decryption of SPA packets.
- Supports HMAC authenticated encryption for both Rijndael and GnuPG. The order of operation is encrypt-then-authenticate to avoid various cryptanalytic problems.
- Replay attacks are detected and thwarted by SHA-256 digest comparison of valid incoming SPA packets. Other digest algorithms are also supported, but SHA-256 is the default.
- SPA packets are passively sniffed from the wire via libpcap. The fwknopd server can also acquire packet data from a file that is written to by a separate Ethernet sniffer (such as with
tcpdump -w <file>), from the iptables ULOG pcap writer, or directly via a UDP socket in--udp-servermode. - For iptables firewalls, ACCEPT rules added by fwknop are added and deleted (after a configurable timeout) from custom iptables chains so that fwknop does not interfere with any existing iptables policy that may already be loaded on the system.
- Supports inbound NAT connections for authenticated SPA communications (iptables firewalls only for now). This means fwknop can be configured to create DNAT rules so that you can reach a service (such as SSH) running on an internal system on an RFC 1918 IP address from the open Internet. SNAT rules are also supported which essentially turns fwknopd into a SPA-authenticating gateway to access the Internet from an internal network.
- Multiple users are supported by the fwknop server, and each user can be assigned their own symmetric or asymmetric encryption key via the /etc/fwknop/access.conf file.
- Automatic resolution of external IP address via https://www.cipherdyne.org/cgi-bin/myip (this is useful when the fwknop client is run from behind a NAT device). Because the external IP address is encrypted within each SPA packet in this mode, Man-in-the-Middle (MITM) attacks where an inline device intercepts an SPA packet and only forwards it from a different IP in an effort to gain access are thwarted.
- Port randomization is supported for the destination port of SPA packets as well as the port over which the follow-on connection is made via the iptables NAT capabilities. The later applies to forwarded connections to internal services and to access granted to local sockets on the system running fwknopd.
- Integration with Tor (as described in this DefCon 14 presentation). Note that because Tor uses TCP for transport, sending SPA packets through the Tor network requires that each SPA packet is sent over an established TCP connection, so technically this breaks the “single” aspect of “Single Packet Authorization”. However, Tor provides anonymity benefits that can outweigh this consideration in some deployments.
- Implements a versioned protocol for SPA communications, so it is easy to extend the protocol to offer new SPA message types and maintain backwards compatibility with older fwknop clients at the same time.
- Supports the execution of shell commands on behalf of valid SPA packets.
- The fwknop server can be configured to place multiple restrictions on inbound SPA packets beyond those enforced by encryption keys and replay attack detection. Namely, packet age, source IP address, remote user, access to requested ports, and more.
- Bundled with fwknop is a comprehensive test suite that issues a series of tests designed to verify that both the client and server pieces of fwknop work properly. These tests involve sniffing SPA packets over the local loopback interface, building temporary firewall rules that are checked for the appropriate access based on the testing config, and parsing output from both the fwknop client and fwknopd server for expected markers for each test. Test suite output can easily be anonymized for communication to third parties for analysis.
- fwknop was the first program to integrate port knocking with passive OS fingerprinting. However, Single Packet Authorization offers many security benefits beyond port knocking, so the port knocking mode of operation is generally deprecated.
Building fwknop
This distribution uses GNU autoconf for setting up the build. Please see the INSTALL file for the general basics on using autoconf.
There are some “configure” options that are specific to fwknop. They are (extracted from ./configure –help):
–disable-client Do not build the fwknop client component. The default is to build the client.
–disable-server Do not build the fwknop server component. The default is to build the server.
–with-gpgme support for gpg encryption using libgpgme –with-gpgme-prefix=PFX prefix where GPGME is installed (optional)
–with-gpg=/path/to/gpg Specify path to the gpg executable that gpgme will use [default=check path]
–with-firewalld=/path/to/firewalld Specify path to the firewalld executable
–with-iptables=/path/to/iptables Specify path to the iptables executable
–with-ipfw=/path/to/ipfw Specify path to the ipfw executable [default=check path]
–with-pf=/path/to/pfctl Specify path to the pf executable [default=check path]
–with-ipf=/path/to/ipf Specify path to the ipf executable [default=check path]
Examples:
./configure –disable-client –with-firewalld=/bin/firewall-cmd
./configure –disable-client –with-iptables=/sbin/iptables –with-firewalld=no









.webp)