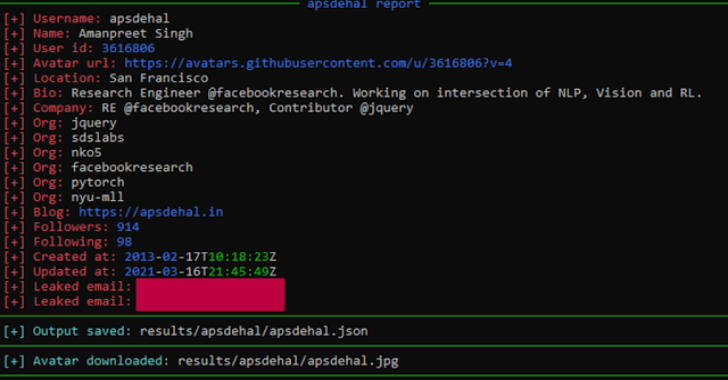
Gitrecon is a OSINT tool to get information from a Github or Gitlab profile and find user’s email addresses leaked on commits.
How does this work?
GitHub uses the email address associated with a GitHub account to link commits and other activity to a GitHub profile. When a user makes commits to public repos their email address is usually published in the commit and becomes publicly accessible, if you know where to look.
GitHub provide some instructions on how to prevent this from happening, but it seems that most GitHub users either don’t know or don’t care that their email address may be exposed.
Finding a GitHub user’s email address is often as simple as looking at their recent events via the GitHub API.
Installation
git clone https://github.com/GONZOsint/gitrecon.git
cd gitrecon/
python3 -m pip install -r requirements.txt
- It is possible to use a Github access token by editing line 3 of the
modules/github_recon.pyfile. This will prevent a possible API ban. - It is possible to use a Gitlab access token by editing line 3 of the
modules/gitlab_recon.pyfile. This will prevent a possible API ban.
token = ‘<Access token here>
Usage
Usage: gitrecon.py [-h] -s {github,gitlab} [-a] [-o] username
Positional Arguments:
username
Optional Arguments:
-h, –help show this help message and exit
-s {github,gitlab} sites selection
-a, –avatar download avatar pic
-o, –output save output
Results are saved in results// path.
Features
Gitlab and Github leaked emails on commits
- Gitlab and Github SSH keys
| Github SSH keys | Gitlab SSH keys |
|---|---|
| ID | ❌ |
| ❌ | Tittle |
| ❌ | Created at |
| ❌ | Expires at |
| Key | Key |
- Gitlab and Github profile info
| Github profile info | Gitlab profile info |
|---|---|
| Username | Username |
| Name | Name |
| User ID | User ID |
| ❌ | State |
| ❌ | Status |
| Avatar url | Avatar url |
| Location | Location |
| Bio | Bio |
| Company | Organization |
| Organizations | ❌ |
| ❌ | Job title |
| ❌ | Work information |
| Blog | Web |
| Gravatar ID | ❌ |
| ❌ | Skype |
| ❌ | |
| Followers | Followers |
| Following | Following |
| Created at | Created at |
| Updated at | ❌ |