Welcome to the ‘Guide-CEH-Practical-Master’, your essential roadmap to mastering the Certified Ethical Hacker (Practical) exam.
Dive deep into the tools, techniques, and insights necessary for success.
Let’s embark on this journey to achieve professional cybersecurity prowess together
Exame Details
- Exam Title: Certified Ethical Hacker (Practical)
- Number of Practical Challenges: 20
- Duration: 6 hours
- Availability: Aspen – iLabs
- Test Format: Cyber Range
- Passing Score: Min 15 Questions
Exam Tips
- Vulnerability analysis to identify security loopholes in the target organization’s network, communication infrastructure, and end systems, etc;
- System hacking, steganography;
- Network scanning to identify live and vulnerable machines in a network;
- OS banner grabbing, service, and user enumeration;
- Different types of cryptography attacks;
- SQL injection attacks;
- Packet sniffing;
- Computer Forensic;
Format
- Realized Test with Web Browser CyberQ
- One ParrotOS to perform the pentest and Windows 11 Machine
- Five machines to compromise on an isolated network from the internet
- Search in Google? (Yes!)
- Talk to someone during the race? (No!)
- Proctored Monitor
Tools
- Nmap
- Hydra
- Sqlmap
- Wpscan
- Nikto
- John
- Hashcat
- Metasploit
- Responder LLMNR
- Wireshark or Tcpdump
- Steghide
- OpenStego
- QuickStego
- Dirb
- OleView
- Dcomcnf
- RpcDump
- Gacutil
- Searchsploit
- sandfly-entropyscan
- Strings
- FTK Imager
- Malwoverview
- GDB or IDA
- Crunch
- Cewl
- LinPeas
- Aircrack-ng
- GTFOBINS
- Veracrypt
- Hashcalc
- Rainbow Crack
- Radare2
- Rockyou and SecList
Helps
- Reddit Exam Reviews
- Medium Exam Reviews
- Professionals Certificate
- Hack The Box (Challenges Steganography and Web)
- Vulnhub (Machines Easy to Medium)
- Labs PenTest Brazil (CEH Course made in Major Eder ft ACADI-TI)
- TryHackMe
- iLabs CEH
- CEH Exam Guide
Examples Questions (There are the real issues)
- What is the IP of the Windows X machine?
- What is the version of the Linux Kernel?
- How many Windows machines are there?
- What is the password for user X of the FTP server?
- What is user X’s IBAN number?
- Which user X’s phone number?
- What is the password hidden in the .jpeg file?
- Rogue AP suspect, crack your password using capture.cap
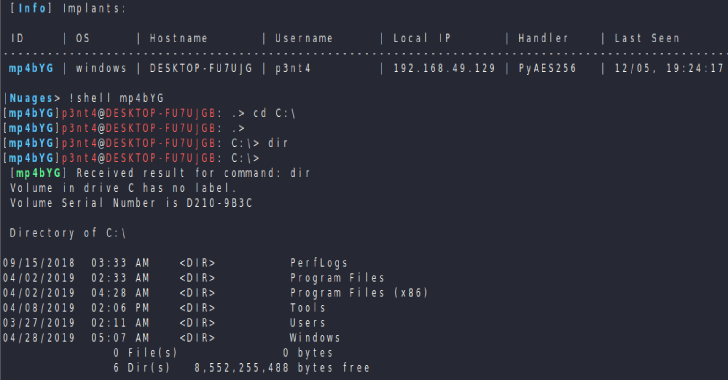
- Discovery RAT in Network and acess computer to recovery secret.txt
- Identify IoT Message using capture.cap
- Identify FQDN of Domain Controller
- Perform deep scan on the elf and obtain hash of the file with highest entropy value.
- Find the executable’s Entry point (Address)
Types of SQL Injection
Union-based SQLi: This technique involves using the UNION SQL operator to combine the results of the original query with the results of an attacker-controlled query.
Error-based SQLi: This technique involves forcing the database to generate an error, which can reveal information about the database structure.
Blind SQLi: In this type of SQLi, the attacker doesn’t get the results of the SQL query in the HTTP response. The attacker has to send a payload, and based on the application’s response, he can infer if the payload was executed successfully or not.
Time-based Blind SQLi: This is a type of blind SQLi where the attacker can infer if the payload was executed successfully or not based on the time the server takes to respond.
Out-of-Band SQLi: In this type of SQLi, the attacker doesn’t get the results of the SQL query in the HTTP response. Instead, the results are sent to an external server controlled by the attacker.
Second Order SQLi: In this type of SQLi, the payload is not directly injected into the SQL query, but it is stored by the application and used in a later SQL query.
Stored Procedure Attacks: This involves calling stored procedures from the SQL injection point.
Function Call Payloads: This involves calling database functions from the SQL injection point.
Boolean-based SQLi: This involves sending a SQL query that will return a different result depending on whether the condition in the query is true or false.
Content-based SQLi: This involves sending a SQL query that will return a different result depending on the content of the HTTP response.
Tools
SQLMap: SQLMap is a popular open-source penetration testing tool that automates the process of detecting and exploiting SQL Injection vulnerabilities.
Havij: Havij is an automated SQL Injection tool that helps penetration testers to find and exploit SQL Injection vulnerabilities.
jSQL Injection: jSQL Injection is a lightweight application used to find database information from a distant server.
BBQSQL: BBQSQL is a blind SQL injection framework written in Python.
NoSQLMap: NoSQLMap is an open-source Python tool designed to audit for as well as automate injection attacks and exploit default configuration weaknesses in NoSQL databases.
SQLNinja: SQLNinja is a tool to exploit SQL Injection vulnerabilities on a web application that uses Microsoft SQL Server as its back-end.
SQLiX: SQLiX is a SQL Injection scanner written in Perl.
SQLSentinel: SQLSentinel is an application-level firewall for MySQL that prevents SQL Injection attacks.
MyBatis: MyBatis is a Java persistence framework that includes a built-in SQL Injection scanner.
Blisqy: Blisqy is a tool to aid Web Security researchers to find Time-based Blind SQL injection on HTTP Headers and also exploitation of the same vulnerability.
Malware Analysis
Static Analysis:
Header Examination: Look at the headers of the executable file. Common executable file formats include PE (Portable Executable) for Windows and ELF (Executable and Linkable Format) for Linux. Disassembly: Disassemble the binary code using a disassembler such as IDA Pro, Ghidra, or Radare2. These tools can help you navigate the assembly code and identify the entry point.
Dynamic Analysis:
Debugger: Use a debugger like OllyDbg, WinDbg, or GDB to run the executable in a controlled environment. Set breakpoints and step through the code until you reach the entry point. Monitoring Tools: Use tools like Process Monitor (ProcMon) on Windows or strace on Linux to monitor system calls and identify when the executable is loaded and starts executing. Strings and Signatures:
String Analysis: Look for strings within the executable that may indicate the entry point. Some malware authors leave identifiable strings. Signature-Based Detection: Use antivirus or anti-malware tools that might have signature databases to identify known malware and their entry points. Code Emulation and Analysis:
Sandboxing: Execute the executable in a controlled environment, often called a sandbox, and monitor its behavior. Analyze the log or output for indications of the entry point.
Tools
Cuckoo Sandbox: An open-source automated malware analysis system.
FireEye: A platform for detecting, preventing, and resolving advanced malware.
Joe Sandbox: A malware analysis platform that provides both static and dynamic analysis.
OllyDbg: A 32-bit assembler level analyzing debugger for Microsoft Windows.
IDA Pro: A multi-processor disassembler and debugger for Windows, Linux, and macOS.
Ghidra: A software reverse engineering framework developed by the NSA.
Radare2: A portable reversing framework that supports a wide range of architectures.
Process Monitor: A monitoring tool for Windows that shows real-time file system, registry, and process/thread activity.
Wireshark: A network protocol analyzer that lets you capture and interactively browse network traffic.
YARA: A tool for identifying and classifying malware based on patterns.
Volatility: A memory forensics framework for incident response and malware analysis.
The Sleuth Kit: A collection of command-line tools for digital investigation and analysis.
Autopsy: A digital forensics platform that provides a graphical interface for The Sleuth Kit.
Mandiant Redline: A free tool for host investigations and memory analysis.
Regshot: A utility that takes a snapshot of your system’s registry and compares it to a second one.
PEiD: A tool that can detect the compiler/packer/cryptor of PE executables.
PEview: A lightweight and portable tool for viewing PE files.
PEStudio: A free tool that performs malware assessments on executable files.
Dependency Walker: A utility that scans any 32-bit or 64-bit Windows module and builds a hierarchical tree diagram of all dependent modules.
VirusTotal: A service that analyzes suspicious files and URLs to detect malware.






.jpg)


.webp)
