This is an example program that can run a Kerberos Key Distribution Center (KDC) on a Windows host and have Windows authenticate to that without joining it to a domain. The code in here is a proof of concept and does not cover all use cases.
How It Works
Contrary to popular belief, Windows does not need to be joined to a domain to work with Kerberos authentication.
If provided with enough information it can attempt to locate the KDC and request the TGT and service ticket from it.
For example if someone attempts to access the fileshare \\server\share with the credential user@contoso.com Windows will attempt to find the KDC for the realm contoso.com.
The DC locator process is documented here but I’ve found that either not all the information is shared or is slightly different in real life.
Based on my investigations I’ve found this is what happens.
- Windows sends a DNS query for the
SRVrecord_kerberos._tcp.dc._msdcs.{realm}{realm}is replaced by the realm in question, for example_kerberos._tcp.dc._msdcs.contoso.com- The
_ldap._tcp.dc._msdcs.{realm}record is also used bynltest.exe /dsgetdcbut SSPI uses_kerberosonly in its lookups - The
LocalKdc.exeprogram sets both so both scenarios works
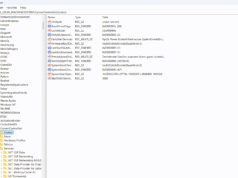
- Windows sends an unauthenticated LDAP search request over UDP to retrieve the domain info
- This is covered in more details under LDAP Ping
- The search request filter is in the form of
(&(DnsDomain=...)(DnsHostName=...)(Host=...)(NtVer=...)) - The
DnsDomainis the realm being requested - The
Hostis the client’s Netbios hostname - The
DnsHostNameis the client’s DNS hostname - The
NtVeris a 32-bit integer flags for NETLOGON_NT_VERSION Options
- The LDAP server replies with a single result with a single attribute called
Netlogoncontaining the domain info- The
NtVerin the request shapes what data structure is returned - On modern systems it is NETLOGON_SAM_LOGON_RESPONSE_EX
- The
Once validated Windows will then use the host returned by the SRV record as the KDC for Kerberos authentication.
When running a local KDC we have all the tools necessary to configure Windows to use a locally running KDC for Kerberos authentication.
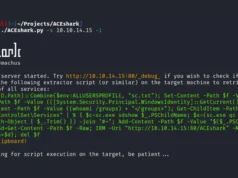
The LocalKdc C# project in this repo runs a DNS, LDAP, and KDC service on localhost and configures the DNS Name Resolution Policy Table (NRPT) to redirect and DNS queries for our realm to the local DNS service.
From there when attempting to authenticate with Kerberos to our realm, Windows will go through the DC locator process with our custom service which just points back to localhost.
The KDC uses Kerberos.NET as the underlying library but any other KDC could theoretically work here.
It should also be possible to edit the code so listening KDC port just tunnel the data to another KDC located elsewhere but that’s outside the scope of this repo.
The DNS NRPT setup is what allows us to point Windows to our local DNS server when querying a custom namespace.
The PowerShell cmdlet Add-DnsClientNrptRule can be used to create these rules manually but this program will do so automatically.
Add-DnsClientNrptRule -Namespace contoso.test, .contoso.test -NameServers 127.0.0.1For more information click here.