Pollenisator is a tool aiming to assist pentesters and auditor automating the use of some tools/scripts and keep track of them.
- Written in python 3
- Provides a modelisation of “pentest objects” : Scope, Hosts, Ports, Commands, Tools etc.
- Tools/scripts are separated into 4 categories : wave, Network/domain, IP, Port
- Objects are stored in a NoSQL DB (Mongo)
- Keep links between them to allow queries
- Objects can be created through parsers / manual input
- Business logic can be implemented (auto vuln referencing, item triggers, etc.)
- Many tools/scripts launch conditions are availiable to avoid overloading the target or the scanner.
- A GUI based on tcl/tk
Documentation
Features
- Register your own tools
- Add command line options in your database.
- Create your own light plugin to parse your tool output.
- Use the objects Models to add, update or delete objects to the pentest inside plugins.
- Limit the number of parallel execution of noisy/heavy tools
- Define a recon/fingerprinting procedure with custom tools
- Choose a period to start and stop the tools
- Define your scope with domains and network IP ranges.
- Custom settings to include new hosts in the scope
- Keep results of all files generated through tools executions
- Start the given docker to implement numerous tools for LAN and Web pentest
- Collaborative pentest
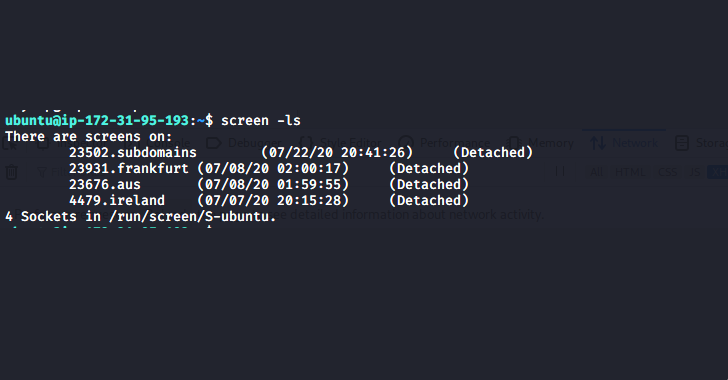
- Split the work between your machines by starting one worker by computer you want to use.
- Tags ip or tools to show your team mates that you powned it.
- Take notes on every object to keep trace of your discoveries
- Follow tools status live
- Search in all your objects properties with the fitler bar.
- have a quick summary of all hosts and their open ports and check if some are powned.
- Reporting
- Create security defects on IPs and ports
- Make your plugins create defects directly so you don’t have to
- Generate a Word report of security defects found. You can use your own template with extra work.
- Generate a Powerpoint report of security defects found. You can use your own template with extra work.
- Shipped with preconfigured tools
- IP / port recon : Nmap (Quick nmaps followed by thorough scan)
- Domain enumeration : Knockpy, Sublist3r, dig reverse, crtsh
- Web : WhatWeb, Nikto, HeaderCollectors, http methods, Dirsearch
- LAN : Crackmapexec, eternalblue and bluekeep scan, smbmap, anonymous ftp, enum4linux
- Unknown ports : amap, nmap scripts
- Misc : ikescan, ssh_scan, openrelay, searchsploit
Setup Guide
This setup guide was originally redacted on ubuntu 16.04 /18.04
- Worker : A worker is a docker / computer where all the tools you want to run are installed. Those worker will launch them on the target and send the resulting data to the server. The name ‘worker’ comes from the use of celery for this part.
- Server : The server is just a mongo database and a SFTP server. Datas are stored in the database and files are kept in the SFTP directory.
- Client : A client is an instance of pollenisator.py. It interacts with the server to launch tools and get data.

There can be 1 or + workers, 1 or + pollenisator client and 1 mongo back end The mongo database and sftp server can be setup with docker or manually installed on windows/linux (linux recommanded)
Worker(s) will run the commands in the queue. You can install the tools you want and do some configuration or use the docker file given.
Pollenisator client will check what command are ready to fire accordingly to a bunch of settings and present to everyone connected the results of the scans.










.webp)
.png)