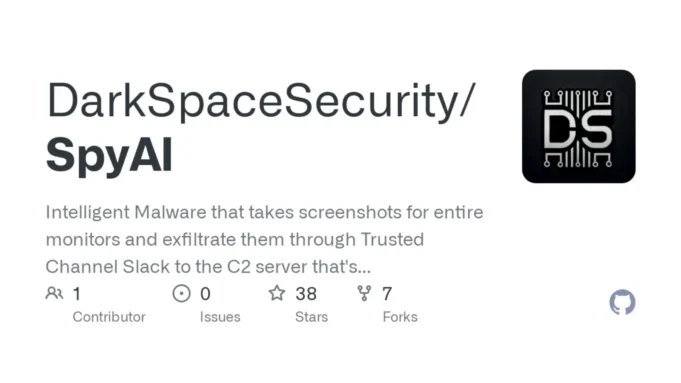
SpyAI is a sophisticated form of malware that leverages advanced technologies to capture and analyze screenshots from entire monitors.
It utilizes Slack as a trusted channel to exfiltrate these screenshots to a Command and Control (C2) server.
The C2 server employs GPT-4 Vision, a cutting-edge AI model, to analyze the screenshots and construct detailed daily activity reports frame by frame.
Key Components And Functionality
- Screenshot Capture and Exfiltration
- SpyAI captures screenshots of entire monitors, providing comprehensive visual data.
- It uses the Slack API to send these screenshots to a C2 server, blending with regular business traffic to evade detection.
- GPT-4 Vision Analysis
- The C2 server utilizes GPT-4 Vision, a multimodal AI model capable of interpreting both text and visual data.
- GPT-4 Vision analyzes the screenshots to identify patterns, objects, and activities, creating detailed activity reports.
- Setup and Configuration
- Python Server Requirements: The setup involves installing necessary Python packages using
pip install slack_sdk requests openai pillow. - Configuration Fields: Users must configure fields like
SLACK_TOKEN,SLACK_CHANNEL_ID,CHECK_INTERVAL, andopenai.api_keyin the Python script.
- Python Server Requirements: The setup involves installing necessary Python packages using
- C++ Integration
- The malware also integrates with C++ components, requiring configuration of
slackTokenandslackChannelin themain.cppfile. - The
Sleepfunction is used to control the interval between operations in milliseconds.
- The malware also integrates with C++ components, requiring configuration of
Implications And Concerns
- Security Risks: SpyAI poses significant security risks due to its ability to evade detection and analyze sensitive visual data.
- AI-Driven Malware Evolution: The use of AI models like GPT-4 Vision in malware represents a new frontier in cybersecurity threats, where malware can adapt and improve its tactics based on real-time analysis.
SpyAI demonstrates the evolving nature of malware, combining AI-driven analysis with sophisticated exfiltration techniques. As AI continues to advance, cybersecurity must adapt to counter these emerging threats effectively.






.jpg)




.webp)