APPLICATIONS
HOT NEWS
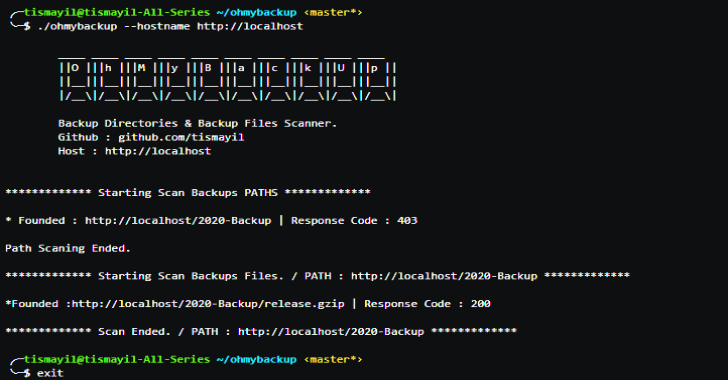
Ohmybackup : Scan Victim Backup Directories & Backup Files
Ohmybackup is to scan victim backup directories & backup files. It scans backup folders on target sites.
Searches archived files in the folders it...
© kalilinuxtutorials.com 2025





.webp)