APPLICATIONS
HOT NEWS
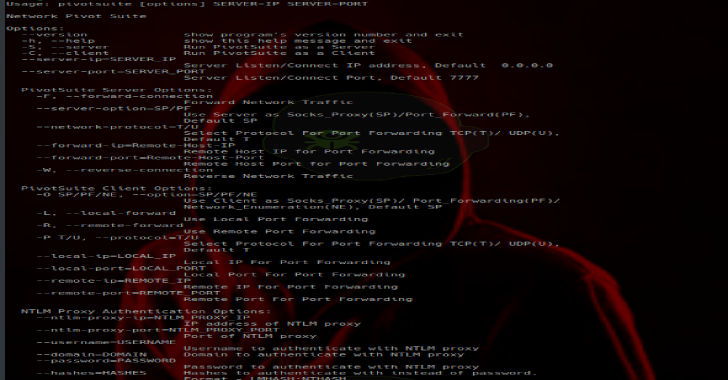
PivotSuite : Network Pivoting Toolkit To Hack The Hidden Network
PivotSuite is a portable, platform independent and powerful network pivoting toolkit, Which helps Red Teamers / Penetration Testers to use a compromised system to...
© kalilinuxtutorials.com 2025