APPLICATIONS
HOT NEWS
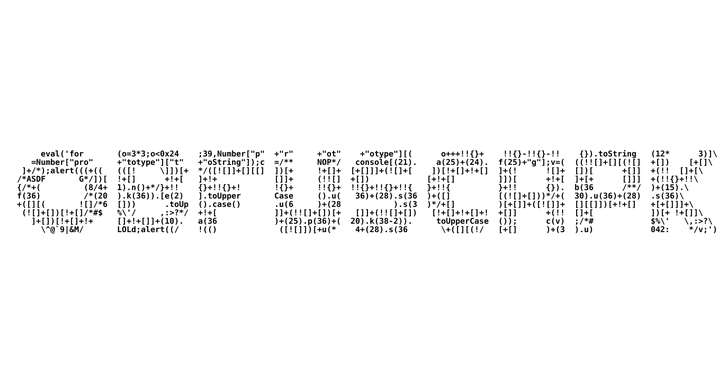
RiskySPN – Collection of PowerShell Scripts Focused on Detecting and Abusing...
RiskySPN is a collection of PowerShell scripts focused on detecting and abusing accounts associated with SPNs (Service Principal Name). This module can assist blue...
© kalilinuxtutorials.com 2025






.png)