APPLICATIONS
HOT NEWS
Vulnerability Research : Harnessing Tools Like Metasploit To Uncover And Mitigate...
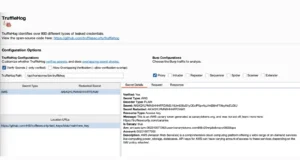
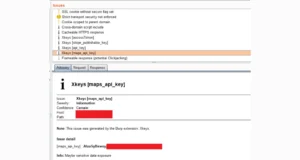
Vulnerability research is a critical aspect of cybersecurity that focuses on identifying, analyzing, and documenting security weaknesses in software, hardware, and networks.
This process...
© kalilinuxtutorials.com 2025