APPLICATIONS
HOT NEWS
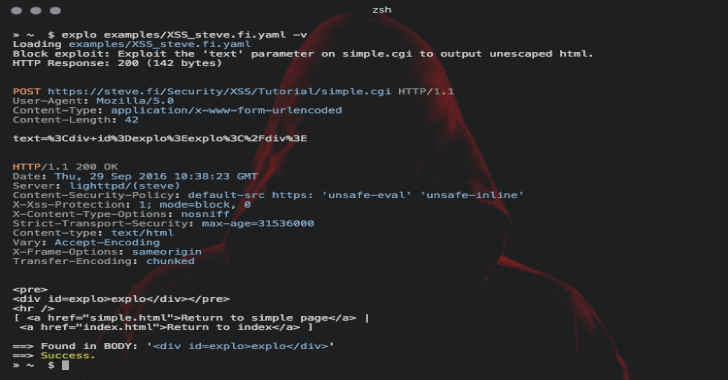
Explo : Human & Machine Readable Web Vulnerability Testing Format
Explo is a simple tool to describe web security issues in a human and machine readable format. By defining a request/condition workflow, explo is...
© kalilinuxtutorials.com 2025