APPLICATIONS
HOT NEWS
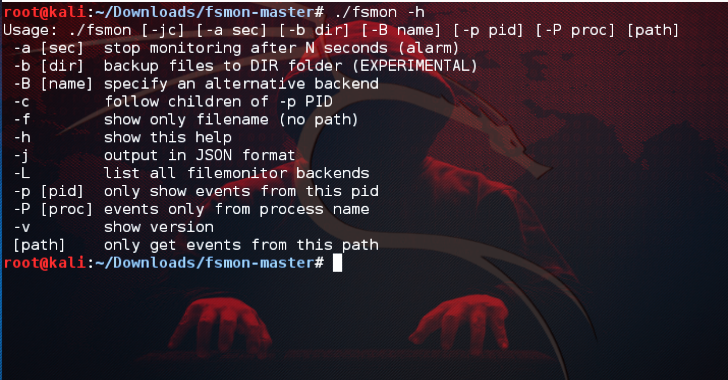
FSMon : Monitor Filesystem On iOS / OS X / Android...
FSMon or FileSystem Monitor utility that runs on Linux, Android, iOS and OSX. Brought to you by Sergi Àlvarez at Nowsecure and distributed under...
© kalilinuxtutorials.com 2025