APPLICATIONS
HOT NEWS
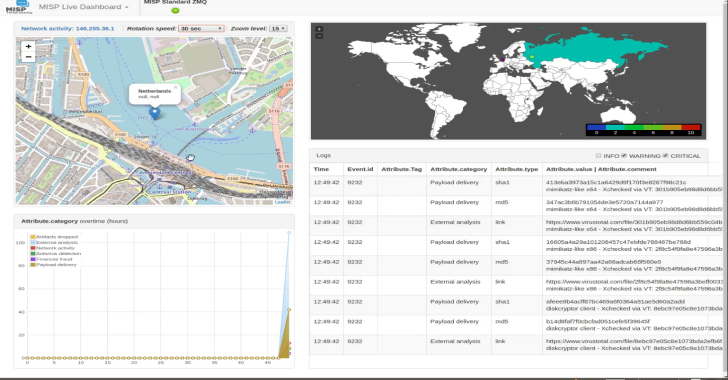
MISP – Dashboard For A Real Time Overview Of Threat Intelligence...
MISP is a dashboard showing live data and statistics from the ZMQ feeds of one or more MISP instances. The dashboard can be used...
© kalilinuxtutorials.com 2025