APPLICATIONS
HOT NEWS
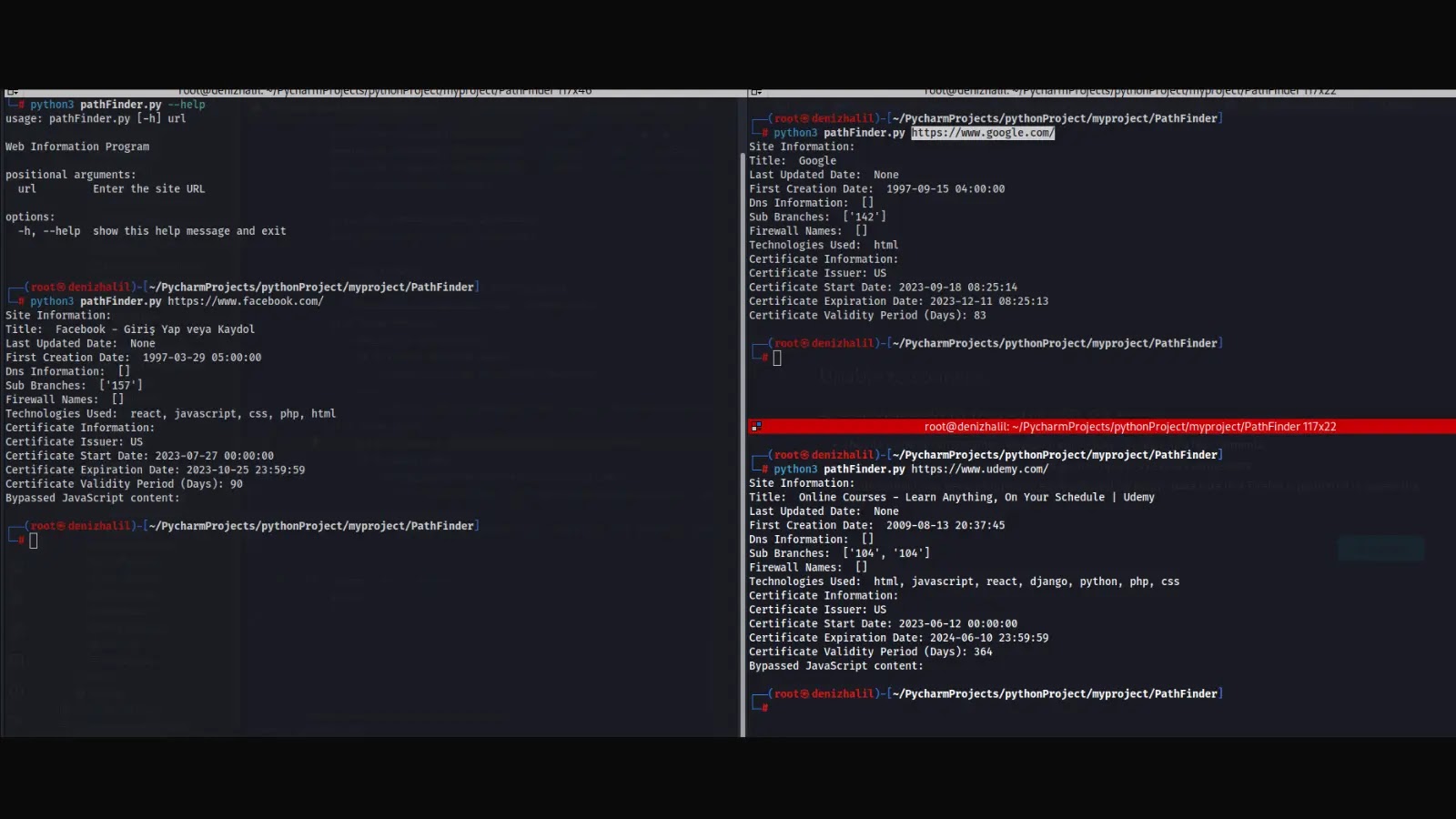
Web Path Finder – Unlocking Website Insights For Comprehensive Web Information
Web Path Finder is a Python program that provides information about a website. It retrieves various details such as page title, last updated date,...
© kalilinuxtutorials.com 2025