APPLICATIONS
HOT NEWS
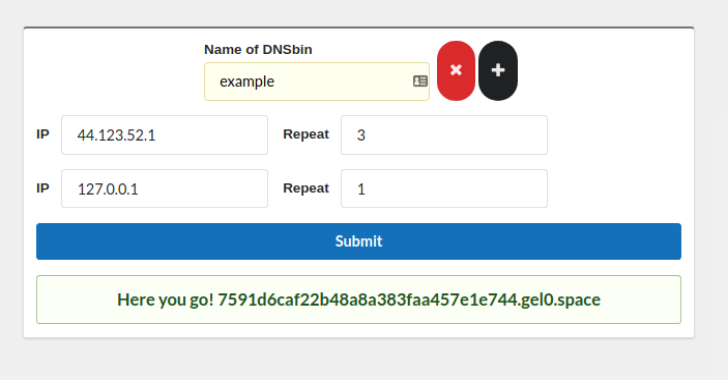
DNSFookup : DNS Rebinding Toolkit
DnsFookup is a DNS Rebinding freamwork containing:
a dns server obviouslyweb api to create new subdomains and control the dns server, view logs, stuff like...
© kalilinuxtutorials.com 2025









.webp)