APPLICATIONS
HOT NEWS
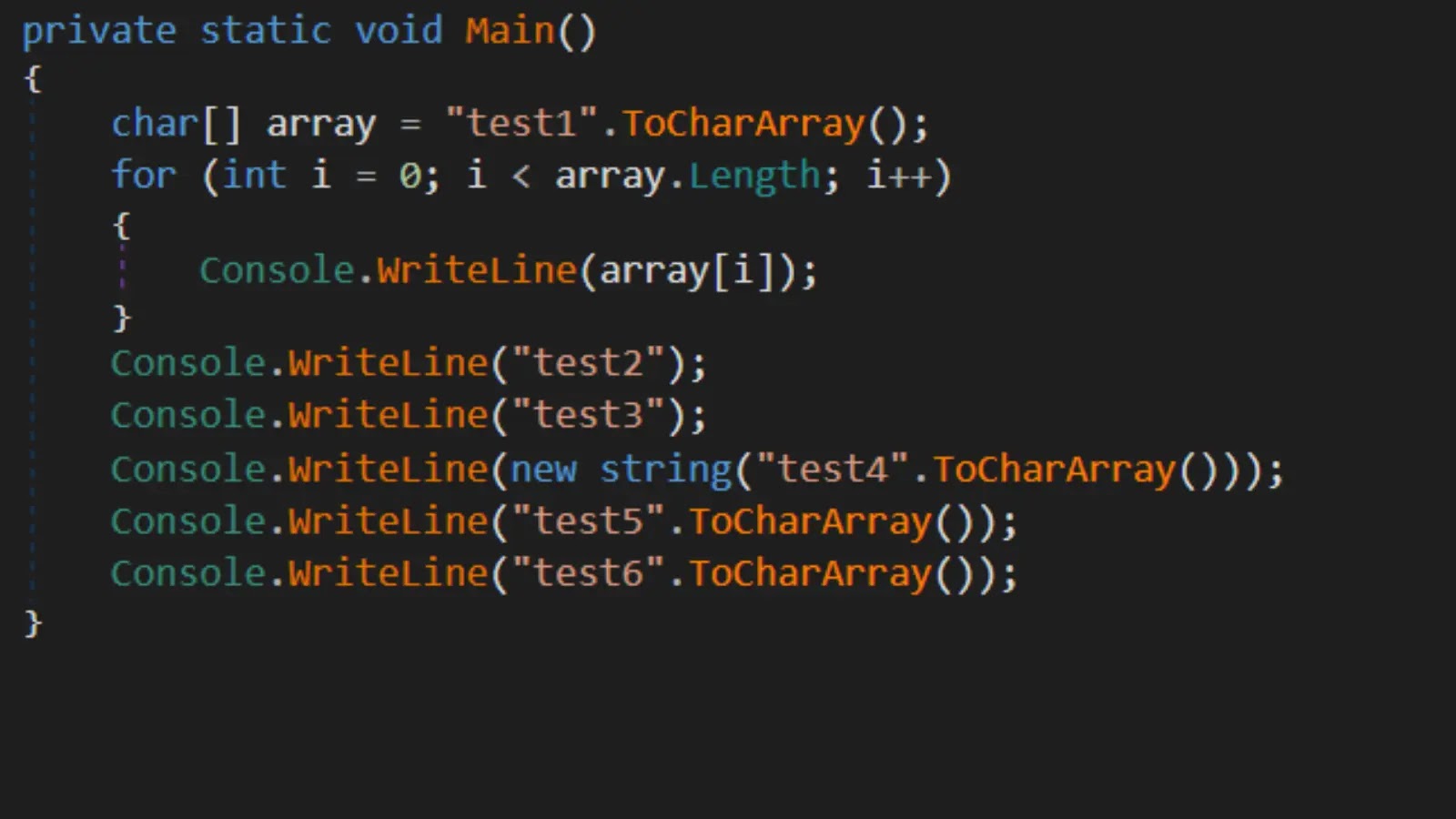
jsluice++ : Enhancing JavaScript Security Analysis With A Comprehensive Guide To...
jsluice++ is an innovative Burp Suite extension that enhances the scanning of JavaScript traffic through both passive and active methods.
By leveraging the jsluice...
© kalilinuxtutorials.com 2025