APPLICATIONS
HOT NEWS
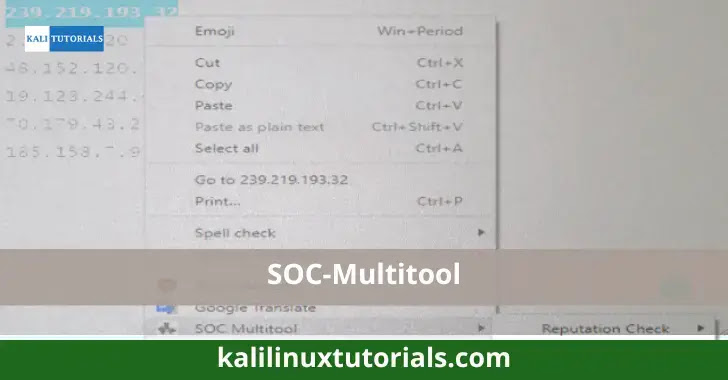
SOC-Multitool
Aman Mishra - 0
Introduction
Introducing SOC Multitool a free and open-source browser extension that accelerates and optimizes research.
Now accessible through the Chrome Web Store and working with every...
© kalilinuxtutorials.com 2025






.webp)



.webp)


.webp)
.webp)