APPLICATIONS
HOT NEWS
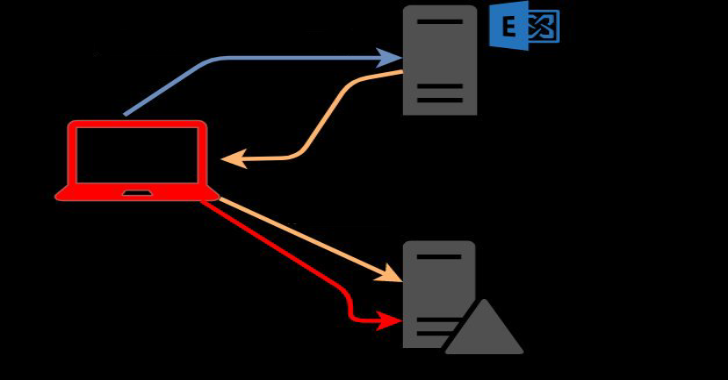
PrivExchange : Exchange Your Privileges For Domain Admin Privs By Abusing...
PrivExchange is a tool to Exchange your privileges for Domain Admin privs by abusing Exchange. These tools require impacket. You can install it from pip...
© kalilinuxtutorials.com 2025






.webp)
.webp)


.webp)
.webp)

.webp)