APPLICATIONS
HOT NEWS
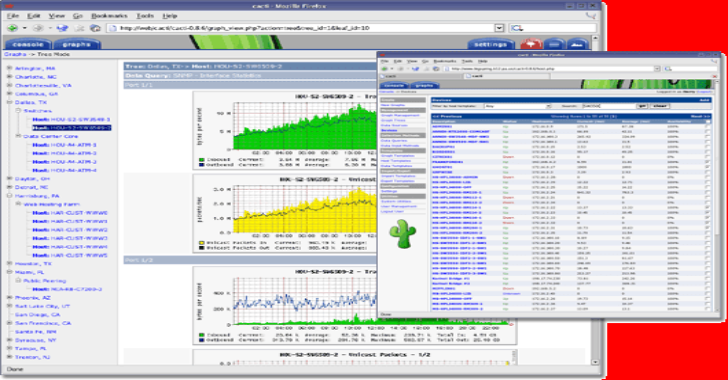
Cacti : Complete Network Graphing Solution
Cacti is a complete network graphing solution designed to harness the power of RRDtool's data storage and graphing functionality providing the following features:
Remote and...
© kalilinuxtutorials.com 2025





.webp)