APPLICATIONS
HOT NEWS
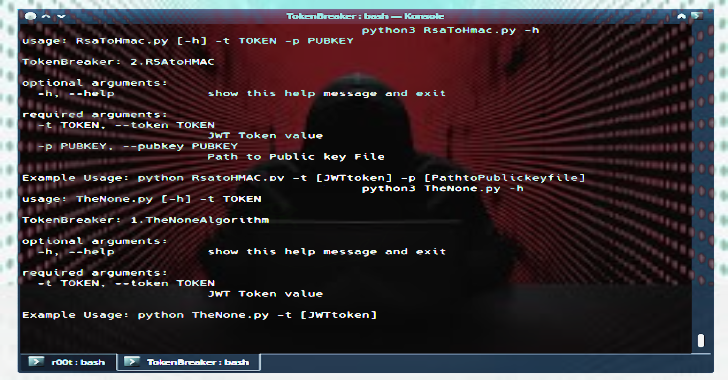
Token Breaker : JSON RSA To HMAC & None Algorithm Vulnerability...
Token Breaker is focused on 2 particular vulnerability related to JWT tokens.
None AlgorithmRSAtoHMAC
Refer to this link about insights of the vulnerability and how an...
© kalilinuxtutorials.com 2025