APPLICATIONS
HOT NEWS
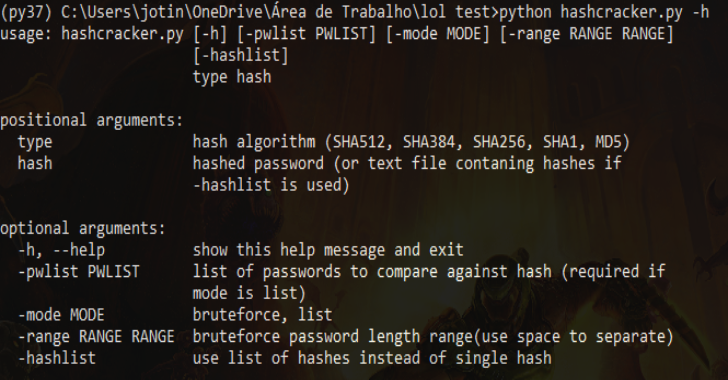
Yin Omega – The Ultimate Toolkit For Cybersecurity Professionals
Public Release which includes useful tools for Hacking, Cracking, OSINT. This project is developed in C# Winforms, leveraging the UI framework from SkeetUI.
While the...
© kalilinuxtutorials.com 2025