APPLICATIONS
HOT NEWS
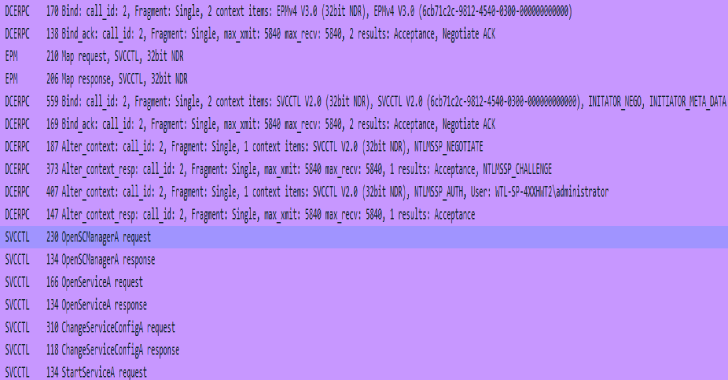
SCShell : Fileless Lateral Movement Tool That Relies On ChangeServiceConfigA To...
SCShell is a fileless lateral movement tool that relies on ChangeServiceConfigA to run commands. The beauty of this tool is that it does not...
© kalilinuxtutorials.com 2025