APPLICATIONS
HOT NEWS
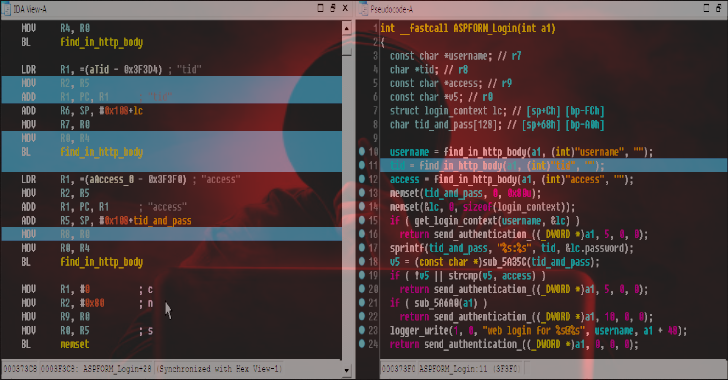
5 Essential Recovery Steps after a Trojan Horse Virus Attack
The best form of defense against a Trojan horse attack is prevention. Always ensure that the emails, websites, and links you open are authentic...
© kalilinuxtutorials.com 2025