APPLICATIONS
HOT NEWS
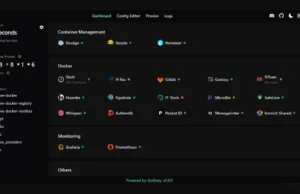
GoDoxy : A Lightweight Reverse Proxy Tool
GoDoxy is a lightweight, straightforward, and high-performance reverse proxy tool written in the Go programming language. It is designed to simplify managing web traffic,...
© kalilinuxtutorials.com 2025