APPLICATIONS
HOT NEWS
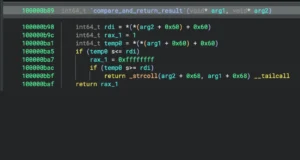
Kam1n0 : Assembly Analysis Platform
Kam1n0 v2.x is a scalable assembly management and analysis platform. It allows a user to first index a (large) collection of binaries into different repositories...
© kalilinuxtutorials.com 2025












.png)