APPLICATIONS
HOT NEWS
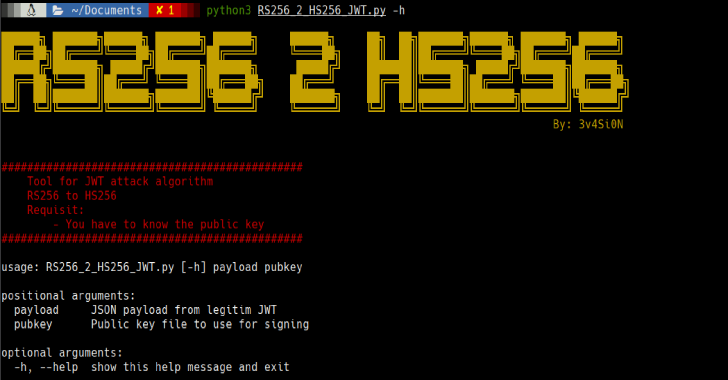
RS256-2-HS256 : JWT Attack To Change Algorithm RS256 to HS256
RS256-2-HS256 is a JWT Attack to change the algorithm RS256 to HS256.
Usage
Usage: RS256_2_HS256_JWT.py payload pubkeyPositional Arguments: payload JSON payload from JWT to attack...
© kalilinuxtutorials.com 2025