APPLICATIONS
HOT NEWS
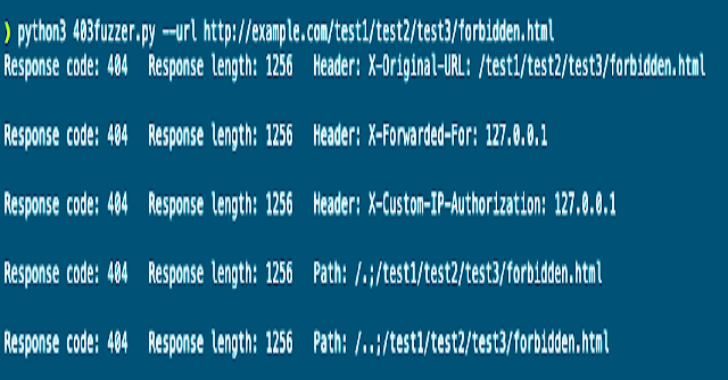
403Fuzzer : Fuzz 403/401Ing Endpoints For Bypasses
403Fuzzer will check the endpoint with a couple of headers such as X-Forwarded-For
It will also apply different payloads typically used in dir traversals, path normalization...
© kalilinuxtutorials.com 2025