APPLICATIONS
HOT NEWS
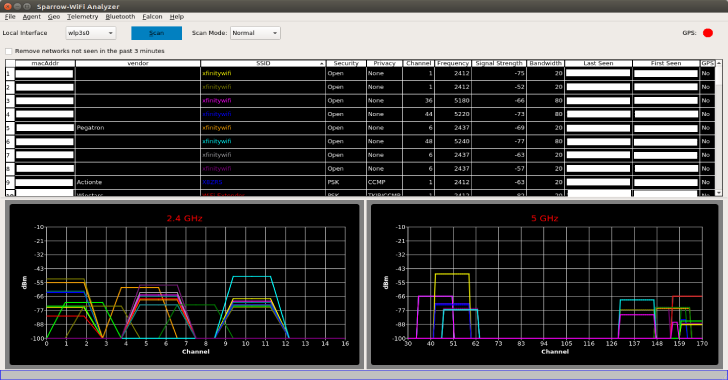
Sparrow WiFi : Next-Gen GUI-based WiFi & Bluetooth Analyzer for Linux
Sparrow WiFi has been built from the ground up to be the next generation 2.4 GHz and 5 GHz WiFi spectral awareness tool....
© kalilinuxtutorials.com 2025













.webp)
.webp)