APPLICATIONS
HOT NEWS
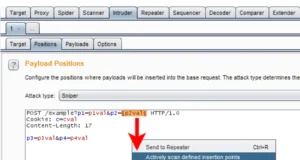
Striker : A Command And Control (C2)
Striker is a simple Command and Control (C2) program.
This project is under active development. Most of the features are experimental, with more to come....
© kalilinuxtutorials.com 2025