APPLICATIONS
HOT NEWS
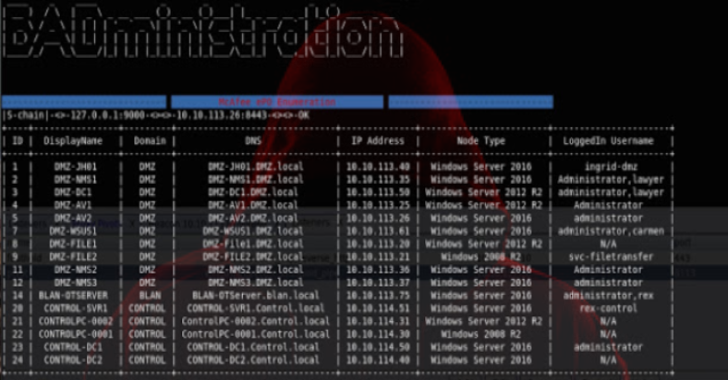
BADministration : Tool Which Interfaces with Management or Administration Applications
BADministration is a tool which interfaces with management or administration applications from an offensive standpoint.
It attempts to provide offsec personnel a tool with...
© kalilinuxtutorials.com 2025








.webp)




.webp)