APPLICATIONS
HOT NEWS
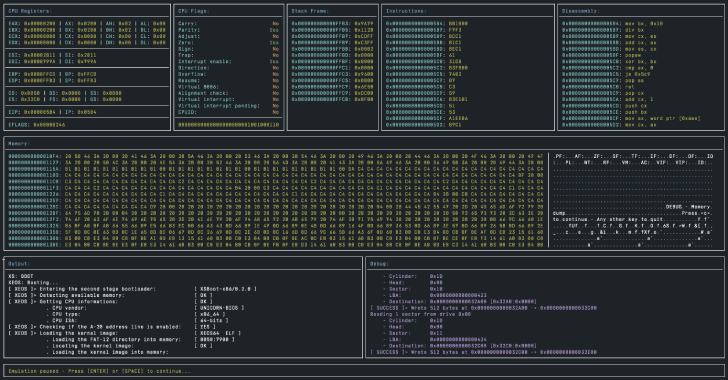
Unicorn-Bios : Basic BIOS Emulator for Unicorn Engine
Unicorn-Bios is a basic BIOS emulator/debugger for Unicorn Engine.
Usage
Usage: unicorn-bios BOOT_IMGOptions: --help / -h: Displays help.--memory / -m: The...
© kalilinuxtutorials.com 2025