APPLICATIONS
HOT NEWS
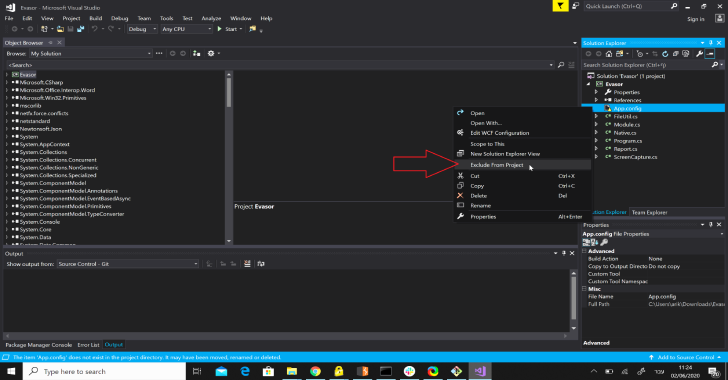
ImpulsiveDLLHijack : C# Based Tool Which Automates The Process Of Discovering...
ImpulsiveDLLHijack is a C# based tool which automates the process of discovering and exploiting DLL Hijacks in target binaries. The Hijacked paths discovered can...
© kalilinuxtutorials.com 2025