APPLICATIONS
HOT NEWS
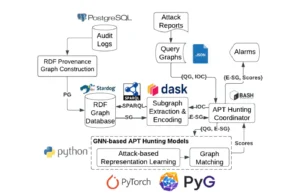
MEGR-APT : Harnessing Graph Neural Networks For Advanced Threat Detection
MEGR-APT is an advanced and scalable system designed for hunting Advanced Persistent Threats (APTs) by identifying suspicious subgraphs that align with specific attack scenarios,...
We provide you with the latest Kali Linux & Penetration testing tools.
Contact us: admin@kalilinuxtutorials.com
© @Kali Linux Tutorials - 2025

















.png)