APPLICATIONS
HOT NEWS
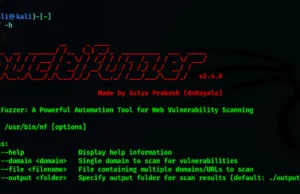
NucleiFuzzer = Nuclei + Paramspider + waybackurls + gauplus + hakrawler...
NucleiFuzzer is an advanced automation tool designed to streamline and optimize web application security testing by integrating a suite of powerful URL discovery and...
© kalilinuxtutorials.com 2025





.webp)