APPLICATIONS
HOT NEWS
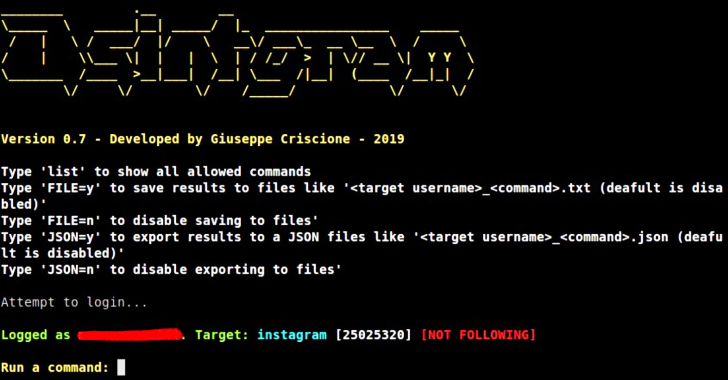
Osintgram – A OSINT Tool On Instagram
Osintgram is a OSINT tool on Instagram. It offers an interactive shell to perform analysis on Instagram account of any users by its nickname....
© kalilinuxtutorials.com 2025