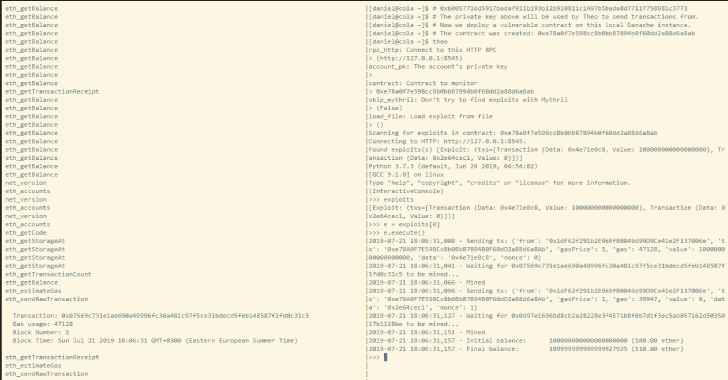
Theo aims to be an exploitation framework and a blockchain recon and interaction tool.
Features
- Automatic smart contract scanning which generates a list of possible exploits.
- Sending transactions to exploit a smart contract.
- Transaction pool monitor.
- Web3 console
- Frontrunning and backrunning transactions.
- Waiting for a list of transactions and sending out others.
- Estimating gas for transactions means only successful transactions are sent.
- Disabling gas estimation will send transactions with a fixed gas quantity.
Theo’s purpose is to fight script kiddies that try to be leet hackers. He can listen to them trying to exploit his honeypots and make them lose their funds, for his own gain.
Install
Theo is available as a PyPI package:
$ pip install theo
$ theo –help
usage: theo [-h] [–rpc-http RPC_HTTP] [–rpc-ws RPC_WS] [–rpc-ipc RPC_IPC]
[–account-pk ACCOUNT_PK] [–contract ADDRESS]
[–skip-mythril SKIP_MYTHRIL] [–load-file LOAD_FILE] [–version]
Monitor contracts for balance changes or tx pool.
Optional arguments:
-h, –help show this help message and exit
–rpc-http RPC_HTTP Connect to this HTTP RPC (default:
http://127.0.0.1:8545)
–account-pk ACCOUNT_PK The account’s private key (default: None)
–contract ADDRESS Contract to monitor (default: None)
–skip-mythril SKIP_MYTHRIL Don’t try to find exploits with Mythril (default: False)
–load-file LOAD_FILE Load exploit from file (default: )
–version show program’s version number and exit
RPC connections:
–rpc-ws RPC_WS Connect to this WebSockets RPC (default: None)
–rpc-ipc RPC_IPC Connect to this IPC RPC (default: None)
Also Read – W13Scan : Passive Security Scanner Linux/Windows/Mac Systems
Install from sources
$ git clone https://github.com/cleanunicorn/theo
$ cd theo
$ virtualenv ./venv
$ . ./venv/bin/activate
$ pip install -r requirements.txt
$ pip install -e .
$ theo –help
Requirements
- Python 3.5 or higher.
- An Ethereum node with RPC available. Ganache works really well for testing or for validating exploits.
Scan a smart contract, find exploits, exploit it:
- Start Ganache as our local Ethereum node
- Deploy the vulnerable contract (happens in a different window)
- Scan for exploits
- Run exploit
Frontrun victim
Setup a honeypot, deploy honeypot, wait for attacker, frontrun:
- Start geth as our local Ethereum node
- Start mining
- Deploy the honeypot
- Start Theo and scan the mem pool for transactions
- Frontrun the attacker and steal his ether