Reconmap is a vulnerability assessment and penetration testing (VAPT) platform. It helps software engineers and infosec pros collaborate on security projects, from planning, to implementation and documentation. The tool’s aim is to go from recon to report in the least possible time.
Requirements
- Docker
- Docker compose
Go to https://reconmap.org to find the user, admin and developer manuals.
Open-Source Vulnerability Assessment And Pentesting Management Platform

Reconmap is an open-source collaboration platform for InfoSec professionals that allows them to plan, execute and document all phases of penetration test projects for multiple targets and clients.
#vulnerability-management #penetration-testing #vapt
History
There is an unwritten rule that says that after doing something manually for the third time, you should automate it. We reached out to the same conclusion after completing our 4th or 5th pentest report. There is a lot of boilerplate and repetition that could be saved should a tool for managing security projects and their reports exist. We looked around for such tool on the open source community and to our surprise there weren’t many complete pentest report generation tools, with the level of documentation, support, and feature set that we were looking for.
That’s our history, we were born to get rid of some unnecessary tedious work in an elegant way. We hope to provide some value to all the infosec professionals (individuals or teams) who are finding themselves spending as much time in reporting as in the actual security work.
We picked the Reconmap name for two reasons:
- The pentest work starts typically with the reconnaissance phase (recon for short), and ends with a report of all the vulnerabilities, exploits and recommendations (the map).
- Reconmap contains the word nmap in its name, a tribute to our favourite network mapper tool.
Development
Version control
All the code for Reconmap is in the open. Below are the most important Github links:
- Github organisation
- REST API – PHP backend
- Web client – React frontend
- CLI – Golang command line
- Website – This website
Architecture
The Reconmap architecture is quite simple. We have a RESTful API written in PHP8.4 and a bunch of clients written in React and React native. The information is stored in a MySQL 8.0 server and for background processing and messaging we relay on Rabbitmq.
The command automation is done using the Docker API and a Golang client.

Roadmap
- Version 1
- Version 2
- Version 3
IN DEVELOPMENT
| Release date | April 2020 |
| Tasks | View on github |
- Vulnerability management
- Tasks
- Projects
- Clients
- Templates
- Reports
- REST API
- Docker deployment options
PLANNING
| Release date | October 2020 |
| Tasks | View on github |
- Agents (to run automation without connecting to a terminal)
- AI and Machine Learning. Automatically assign vulnerability scores, detect risks and so on.
- Better analytics.
- Desktop app (Electron based)
- gRPC API
- Kubernetes deployment options
PLANNING
| Release date | February 2021 |
| Tasks | View on github |
- Reporting engine
- Integration with Solr for more powerful search features
- Use of Keycloak for identity management
- Addon marketplace
- (others to be defined)
Troubleshooting
Errors occur for many reasons. From environmental differences, to permissions, to differences in software versions and more. Here you will find some resources that could help you troubleshoot problems with Reconmap. If these notes still leave you facing a problem, reach out to us on Gitter where we will happily assist you.
Server logs show all sort of warnings and errors and should be your first stop while troubleshooting problems with Reconmap. Its location is /var/log/nginx/error.log inside the backend API Docker container.
If you want to see the last lines of this file run the following Docker command:
$ docker exec reconmap-backend-api tail /var/log/nginx/error.log
Example output
#0 /var/www/webapp/src/Services/ConfigLoader.php(12): json_decode()
#1 /var/www/webapp/public/index.php(26): Reconmap\Services\ConfigLoader->loadFromFile()
#2 {main}
thrown in /var/www/webapp/src/Services/ConfigLoader.php on line 12″ while reading response header from upstream, client: 172.19.0.1, server: localhost, request: “OPTIONS /users/login HTTP/1.1”, upstream: “fastcgi://unix:/var/run/php/php7.4-fpm.sock:”, host: “localhost:8080”, referrer: “http://localhost:3001/login”
2020/10/29 19:40:11 [error] 25#25: *54 FastCGI sent in stderr: “PHP message: PHP Warning: file_get_contents(/var/www/webapp/config.json): failed to open stream: No such file or directory in /var/www/webapp/src/Services/ConfigLoader.php on line 12PHP message: PHP Stack trace:PHP message: PHP 1. {main}() /var/www/webapp/public/index.php:0PHP message: PHP 2. Reconmap\Services\ConfigLoader->loadFromFile() /var/www/webapp/public/index.php:26PHP message: PHP 3. file_get_contents() /var/www/webapp/src/Services/ConfigLoader.php:12PHP message: PHP Fatal error: Uncaught TypeError: json_decode() expects parameter 1 to be string, bool given in /var/www/webapp/src/Services/ConfigLoader.php:12
Stack trace:
#0 /var/www/webapp/src/Services/ConfigLoader.php(12): json_decode()
#1 /var/www/webapp/public/index.php(26): Reconmap\Services\ConfigLoader->loadFromFile()
#2 {main}
thrown in /var/www/webapp/src/Services/ConfigLoader.php on line 12″ while reading response header from upstream, client:
Application logs
After the sever logs come the application logs. Its location is API_FOLDER/logs/application.log and similarly to the server logs, here you can see warnings and errors generated by the API or the backend jobs.
Example output
[2020-10-29 12:26:01] cron.DEBUG: Running queue processor {“class”:”Reconmap\Tasks\EmailTaskProcessor”} []
[2020-10-29 12:26:01] cron.DEBUG: Running queue processor {“class”:”Reconmap\Tasks\TaskResultProcessor”} []
[2020-10-29 12:26:21] http.WARNING: Expired token [] []
[2020-10-29 12:26:21] http.WARNING: Expired token [] []
[2020-10-29 12:26:21] http.WARNING: Expired token [] []
Features
- Simple dashboard with analytics
- Search across all your data (projects, vulnerabilities, tasks, …)
- Users and roles (including client access to projects)
- Two-factor authentication (2FA/MFA, TOPT)
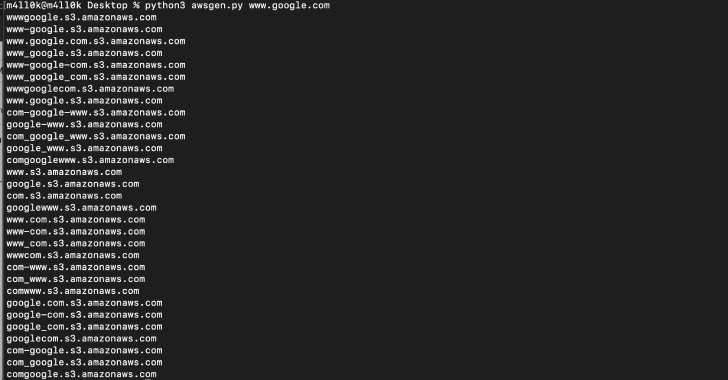
- Security commands database and automation
- Vulnerability database
- Tasks manager
- Project and templates
- Client management
- Export/import data
- Notes with markdown support
- Attachments (docs, screenshots) to projects, vulnerabilities and tasks
- Rest API: to easily integrate Reconmap with external tools and scripts.
- Custom (whitelabel) report generation (HTML, PDF)
- Audit log
- Extensible via plugins
- Web and mobile clients
- Dark/Light themes
- Free and open source
- And more!
Integrations
| Integration | URL |
|---|---|
| Acunetix | https://twitter.com/acunetix |
| Amap | https://www.thc.org/thc-amap/ |
| Arachni | https://twitter.com/ArachniScanner |
| arp-scan | http://linux.die.net/man/1/arp-scan |
| BeEF | https://twitter.com/beefproject |
| Brutexss | https://github.com/rajeshmajumdar/BruteXSS |
| Burp, BurpPro | https://twitter.com/Burp_Suite |
| Core Impact, Core Impact | https://twitter.com/CoreSecurity |
| Dig | |
| Dirb | http://tools.kali.org/web-applications/dirb |
| Dirsearch | |
| Dnsenum | https://github.com/fwaeytens/dnsenum |
| Dnsmap | https://github.com/makefu/dnsmap |
| Dnsrecon | https://github.com/darkoperator/dnsrecon |
| Dnswalk | https://github.com/leebaird/discover |
| evilgrade | http://twitter.com/infobytesec |
| Fierce | http://tools.kali.org/information-gathering/fierce |
| Fruitywifi | http://www.fruitywifi.com/index_eng.html |
| ftp | |
| Goohost | http://www.aldeid.com/wiki/Goohost |
| hping3 | http://tools.kali.org/information-gathering/hping3 |
| Hydra | https://www.thc.org/thc-hydra |
| Immunity Canvas | http://www.immunityinc.com/products/canvas/ |
| Ip360 | |
| Lynis | https://cisofy.com/lynis/ |
| Listurls | |
| Maltego | https://www.paterva.com/web6/products/maltego.php |
| masscan | https://twitter.com/ErrataRob |
| Medusa | http://h.foofus.net/?page_id=51 |
| Metagoofil | https://code.google.com/p/metagoofil/downloads/list |
| Metasploit | https://twitter.com/metasploit |
| Ndiff | https://nmap.org/ndiff/ |
| Nessus | https://twitter.com/tenablesecurity |
| Netcat | http://netcat.sourceforge.net/ |
| Netdiscover | |
| Netsparker | https://twitter.com/Netsparker |
| Netsparker Cloud | |
| Nexpose, Nexpose Enterprise | https://twitter.com/rapid7 |
| Nikto | https://cirt.net/Nikto2 |
| Nmap | https://twitter.com/nmap |
| Openvas | https://twitter.com/openvas |
| PasteAnalyzer | https://github.com/Ezequieltbh/pasteAnalyzer |
| Peeping Tom | https://bitbucket.org/LaNMaSteR53/peepingtom/ |
| ping | |
| propecia | http://packetstormsecurity.com/files/14232/propecia.c.html |
| Qualysguard | https://www.qualys.com/ |
| Recon-NG | https://hackertarget.com/recon-ng-tutorial/ |
| Retina | http://www.beyondtrust.com/Products/RetinaNetworkSecurityScanner/ |
| Reverseraider | http://sourceforge.net/projects/complemento/files/ |
| Sentinel | |
| Shodan | https://twitter.com/shodanhq |
| Skipfish | https://code.google.com/p/skipfish/ |
| Sqlmap | https://twitter.com/sqlmap |
| SSHdefaultscan | https://github.com/atarantini/sshdefaultscan |
| SSLcheck | |
| SSLyze | https://github.com/nabla-c0d3/sslyze |
| Sublist3r | https://github.com/aboul3la/Sublist3r |
| Telnet | |
| Theharvester | https://github.com/laramies/theHarvester |
| Traceroute | |
| W3af | https://twitter.com/w3af |
| Wapiti | http://wapiti.sourceforge.net/ |
| Wcscan | |
| Webfuzzer | http://gunzip.altervista.org/g.php?f=projects#webfuzzer |
| WebInspect | https://resources.infosecinstitute.com/webinspect/#gref |
| Wfuzz | https://wfuzz.readthedocs.io/en/latest/index.html |
| whois | |
| WPScan | https://wpscan.org/ |
| Xsssniper | https://github.com/gbrindisi/xsssniper |
| X1, Onapsis | https://twitter.com/onapsis |
| Zap | https://twitter.com/zaproxy |
Demo
The demo server has 4 users to show the different permission levels. The credentials for these users are:
| Username | Password | Role |
|---|---|---|
| admin | admin123 | Administrator |
| su | su123 | Superuser |
| user | user123 | User |
| cust | cust123 | Client |
Watch it working
If you prefer to watch a Reconmap demonstration instead hit the play button below.
Screenshots
Vulnerabilities

Tasks

Project templates

Client form

Audit log

Integrations

How to run locally in 2 easy steps
- First you need to start your docker containers
$ docker-compose up -d
- After this, open your browser at http://localhost:3001