chntpw is a Kali Linux tool that can be used to edit the windows registry, reset a users password, and promote a user to administrator, as well as several other useful options. Using chntpw is a great way to reset a Windows Password or otherwise gain access to a Windows machine when you don’t know what the password it
chntpw is a utility to view some information and change user passwords in a Windows NT/2000, XP, Vista,7 SAM user database file, usually located at \WINDOWS\system32\config\SAM on the Windows file system.
In addition, it contains a simple registry editor (same size data writes) and hex-editor with which the information contained in a registry file can be browsed and modified. Since chntpw is used for accessing and changing passwords, this tool is used for password forensics.
chntpw retrieves information like accounts, account types, password hash etc from the SAM. The tool can alter the values present in SAM to reset the password or to change it. It can also add/remove the lock for an account.
OPTIONS
Syntax: chntpw [OPTIONS] <samfile> [systemfile] [securityfile] [otherreghive]
-h This message -u <user> Username to change, Administrator is default -l list all users in SAM file -i Interactive. List users (as -l) then ask for username to change -e Registry editor. Now with full write support! -d Enter buffer debugger instead (hex editor), -t Trace. Show hexdump of structs/segments. (deprecated debug function) -v Be a little more verbose (for debuging) -L Write names of changed files to /tmp/changed -N No allocation mode. Only (old style) same length overwrites possible
LAB 1: CHANGING THE WINDOWS PASSWORD USING CHNTPW
Scenario:
8GB USB Drive with Kali Linux installed
Windows 7 Machine
Explanation
This is a forensic analysis. So we shouldn’t alter with the filesystem of the target as far as possible. However, we are gonna try & change the password for a copy of the original SAM copied to the Kali Linux desktop. This can be recopied to the original location if you want to reset or change a forgotten password.
The password is stored in SAM file in windows. The Security Accounts Manager (SAM) is a database file in Windows XP, Windows Vista and Windows 7 that stores users’ passwords. It can be used to authenticate local and remote users. Usually, SAM file is located in C/Windows/system32/config/SAM.
For this lab, we have created a Bootable USB with kali Linux installed. Then the following which is described after booting into the forensic mode. For this, you have to change to boot order in your machine & set the USB to boot first. Click here for a detailed documentation on how to do this.
Then we copy the Sam file to kali desktop for this Lab. In the real world, you may not do this.
After that, we are listing all users in the SAM file. For that
command: chntpw –l <sam file>
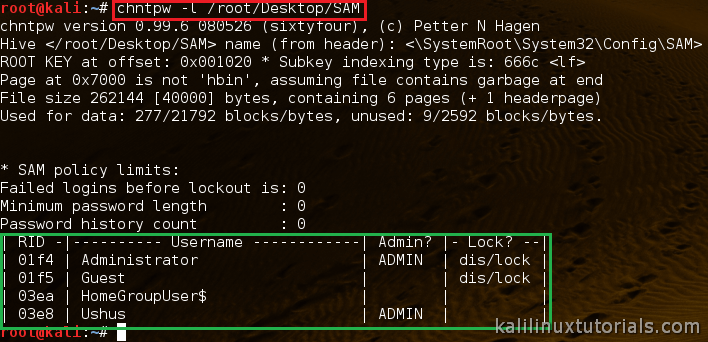
Next, we have to select the username whose password has to be changed. For that the syntax is
command: chntpw –u <user> <sam file>

Now the tool will come to the user edit menu. And then we have to select what we want to do. Just type the number corresponding to our required tasks. Here we are changing the password. So type “2”.
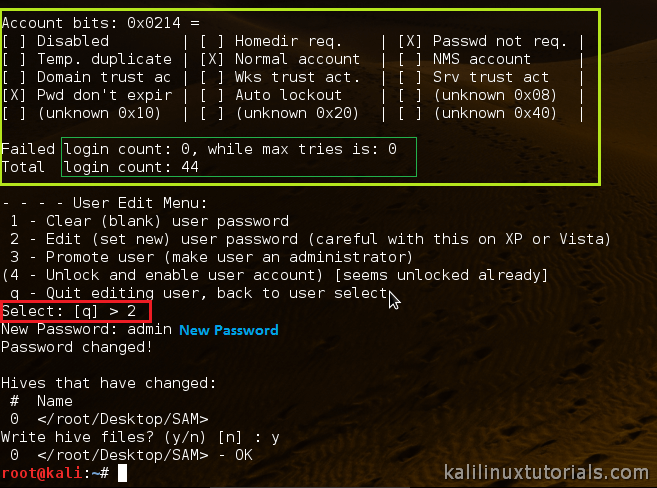
Then the tool will ask to type the new password. Just type it and press enter. Then it will ask if we want to save the password. Press y for saving the new password. Now we have changed the password in the SAM file.
In the real scenario, this is done by live booting Kali Linux forensic cd into the windows system without changing the location of SAM file.