APPLICATIONS
HOT NEWS
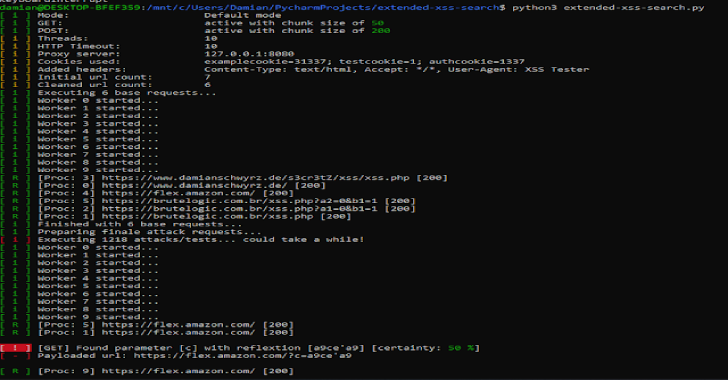
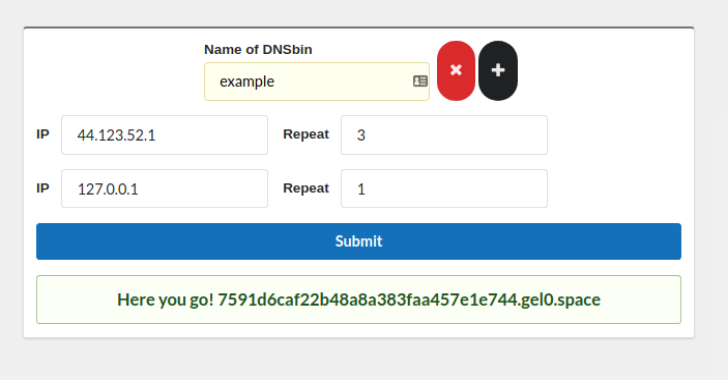
AutoSSRF : Smart Context-Based SSRF Vulnerabiltiy Scanner
AutoSSRF is your best ally for identifying SSRF vulnerabilities at scale. Different from other ssrf automation tools, this one comes with the two following...
© kalilinuxtutorials.com 2025