APPLICATIONS
HOT NEWS
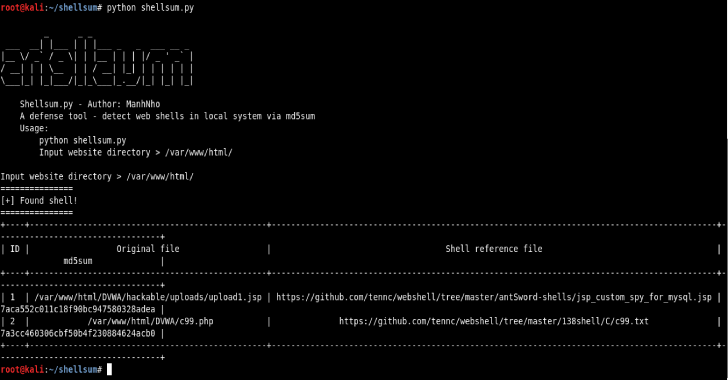
HTBenum : A Linux Enumeration Script For Hack The Box
HTBenum is a Linux enumeration script for Hack The Box. This script is designed for use in situations where you do not have internet...
© kalilinuxtutorials.com 2025