APPLICATIONS
HOT NEWS
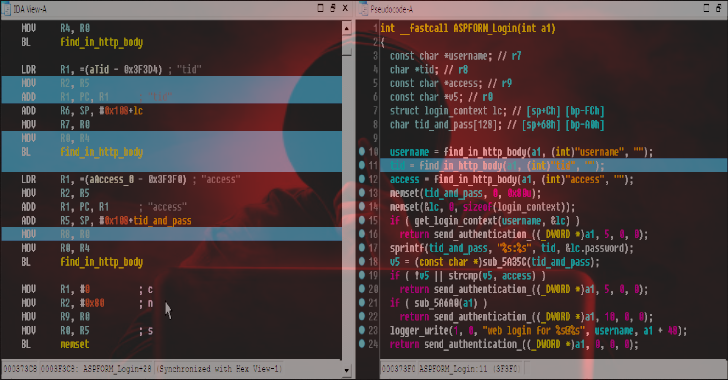
Dsync : IDAPython Plugin That Synchronizes Disassembler & Decompiler Views
Dsync is a IDAPython plugin that synchronizes decompiled and disassembled code views. Please refer to comments in source code for more details.
Also Read -...
© kalilinuxtutorials.com 2025